Home > Aviator > Aviator for SharePoint Online > Permissions Required by Destination SharePoint Online
Download this articlePermissions Required by Destination SharePoint Online
To connect to the destination, you can choose to only use a Fly app profile or custom app profile as the authentication method. You can also use the combination of a service account and a Fly app profile, the combination of a service account and a custom app profile, the combination of a Fly app profile and a (custom) delegated app profile, or the combination of a custom app profile and a (custom) delegated app profile.
Refer to the following sections to view the permissions required by the authentication methods.
Fly App Profile Permissions
With the Tenant Owner or Service Administrator role, you can create a Fly app profile in AvePoint Online Services > Management > App management to connect to the Microsoft 365 tenant using the Fly app.
Refer to Fly App Profile Permissions about how to create a Fly app profile and required permissions of the Fly app profile.
Custom App Profile Permissions
With the Tenant Owner and Service Administrator role, you can create a custom app profile in AvePoint Online Services > Management > App management to connect to the Microsoft 365 tenant using a custom Azure app.
Refer to the following procedures to create a custom app profile:
-
Prepare a certificate in Microsoft Entra ID. Refer to Prepare a Certificate for the Custom Azure App for more information.
You can ignore this step if you have a certificate.
-
Create a custom Azure app in Microsoft Entra ID. Refer to Create Custom Azure Applications for more information.
NOTEIf the destination is a multi-geo tenant, and the destination Microsoft 365 Groups need to be created in a defined location, you need to assign the SharePoint administrator role to the custom Azure app. Refer to the How to Assign the SharePoint Administrator role to an App? section below for instructions.
-
Create an App Profile for a Custom Azure App in AvePoint Online Services.
After you re-authorize the app profile, you need to wait about one hour before using the app profile for your Aviator job to refresh the token if there are permissions updated.
Refer to the following tables to add API permissions required by Aviator for SharePoint Online to the custom Azure app.
| API | Permission | Type | Purpose |
|---|---|---|---|
| Microsoft Graph | User.Read.All (Read all users' full profiles) | Application | Retrieve and migrate Microsoft 365 users. |
| Microsoft Graph | RoleManagement.Read.Directory (Read all directory RBAC settings) | Application | Retrieve and migrate Microsoft global groups. |
| Microsoft Graph | Files.Read.All (Read files in all site collections) | Application | Retrieve channel folders in destination team sites. |
| Microsoft Graph | Group.ReadWrite.All (Read and write all groups) | Application | Retrieve and migrate Microsoft 365 Groups and Group members. The permission is required in the following situations when running Aviator for SharePoint Online jobs: ● Create Microsoft 365 groups and add group members when migrating source team sites related to Microsoft 365 Groups. ● Map source SharePoint Groups (Owners/Members/Visitors) to destination Microsoft 365 Groups and add users to the Microsoft 365 Groups as owners or members when migrating team sites without Microsoft 365 Groups to team sites related to Microsoft 365 Groups. If you want to use Microsoft 365 Groups Migration to migrate the Microsoft 365 Groups to which the team sites belong, you can remove this permission. |
| Microsoft Graph | Sites.Create.All | Application | Create SharePoint sites. |
| SharePoint/Office 365 SharePoint Online | Sites.FullControl.All (Have full control of all site collections) | Application | Retrieve settings and permissions of SharePoint Online site collections. |
| SharePoint/Office 365 SharePoint Online | TermStore.ReadWrite.All (Read and write managed metadata) | Application | Retrieve and migrate Managed Metadata Service. |
| Azure Rights Management Services *Note: For 21Vianet tenants, the API name is Microsoft Rights Management Services. | Content.DelegatedWriter (Create protected content on behalf of a user) | Application | Only required if you want to manage sensitivity labels of files/sites. |
| Azure Rights Management Services *Note: For 21Vianet tenants, the API name is Microsoft Rights Management Services. | Content.Writer (Create protected content) | Application | Only required if you want to manage sensitivity labels of files/sites. |
| Microsoft Information Protection Sync Service | UnifiedPolicy.Tenant.Read (Read all unified policies of the tenant.) | Application | Only required if you want to manage sensitivity labels of files/sites. |
For easy use, you can directly use the following commands to add required API permissions through Manifest for Microsoft 365 Commercial tenants.
How to Assign the SharePoint Administrator role to an App?
To assign the SharePoint administrator role to an app, refer to the following steps:
-
Log in to Microsoft Entra admin center (or Azure portal) and navigate to Microsoft Entra ID.
-
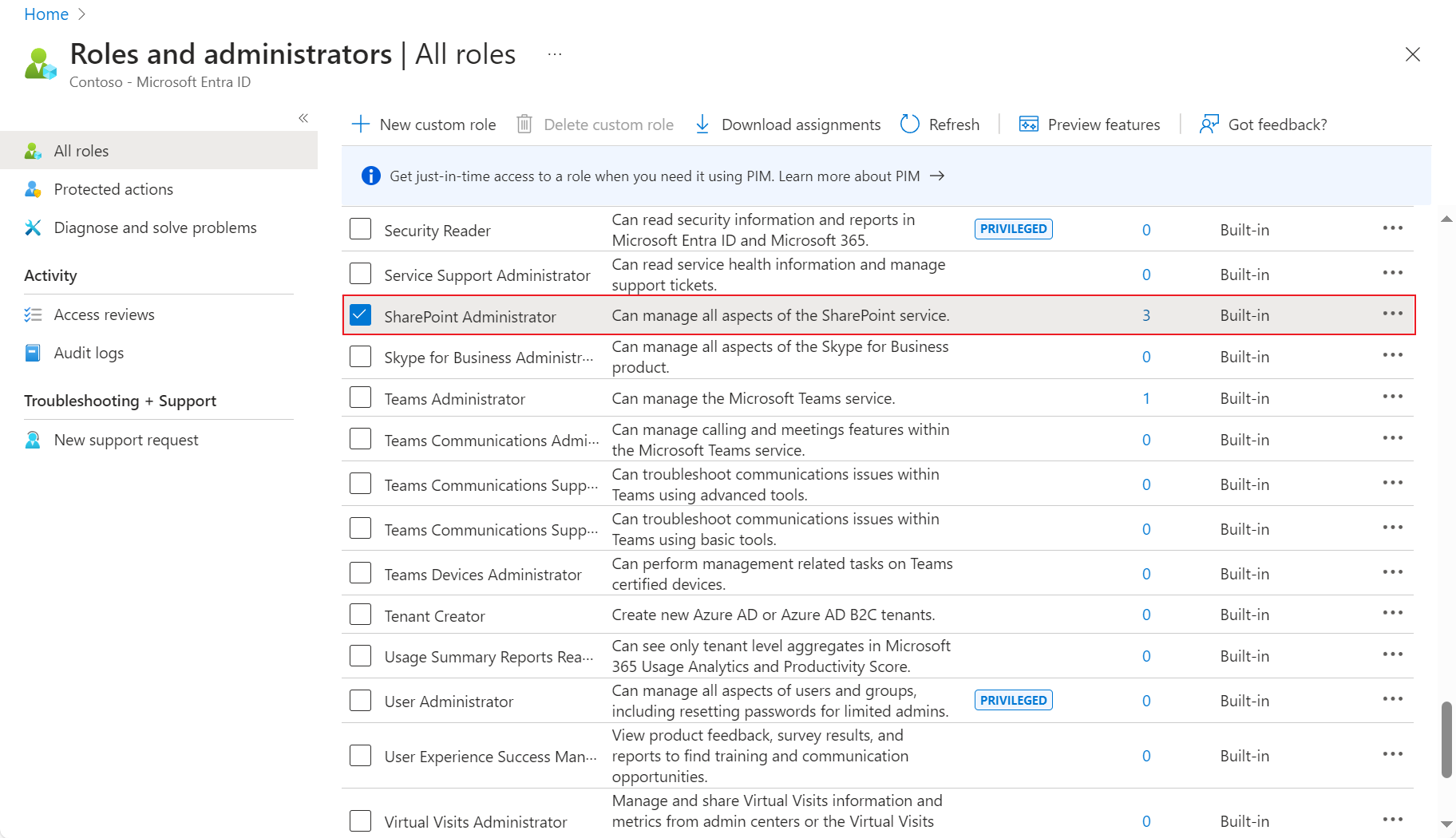
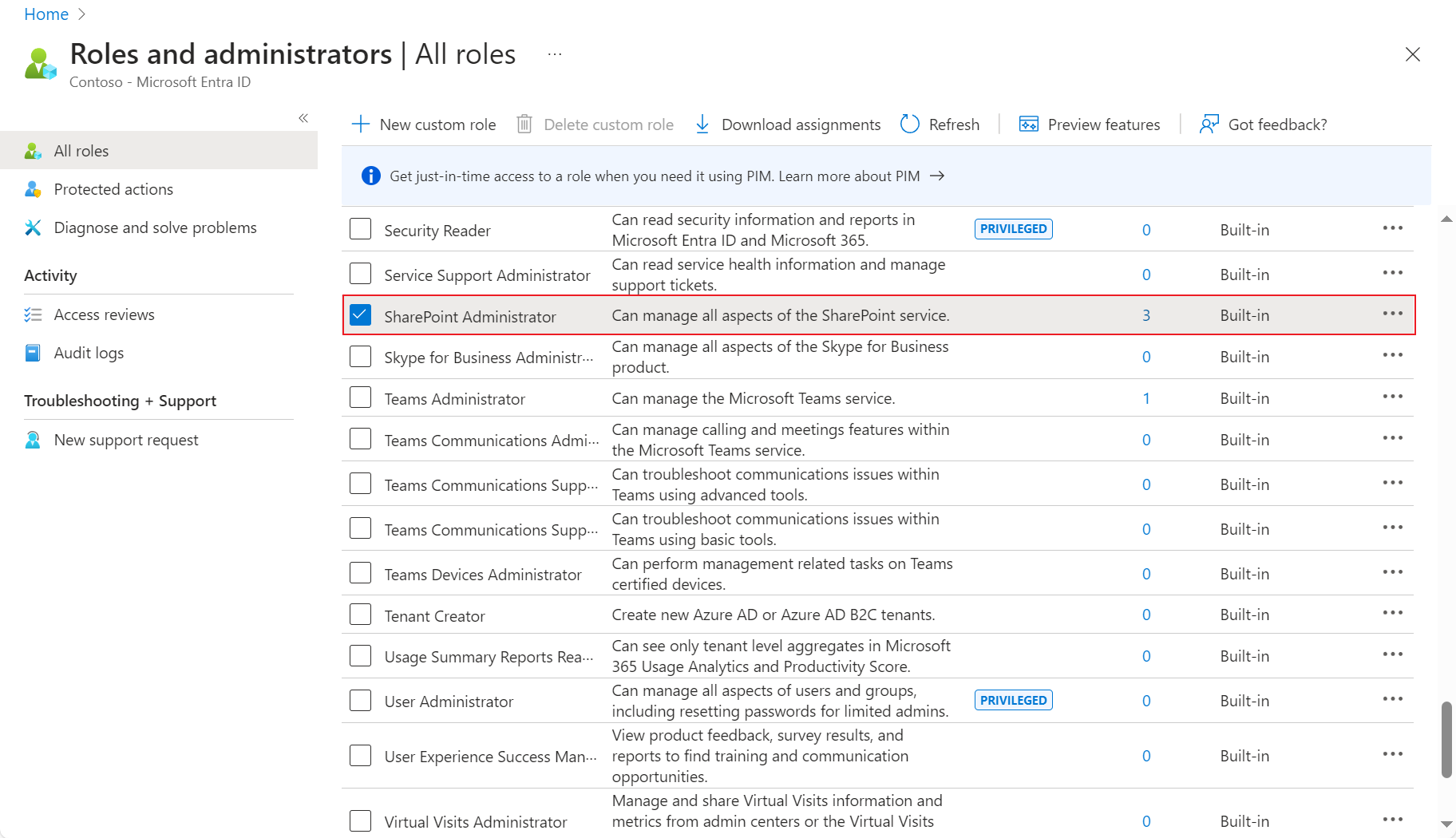
Click Roles & admins (or Roles and administrators) in the left pane, and click SharePoint Administrator.
-
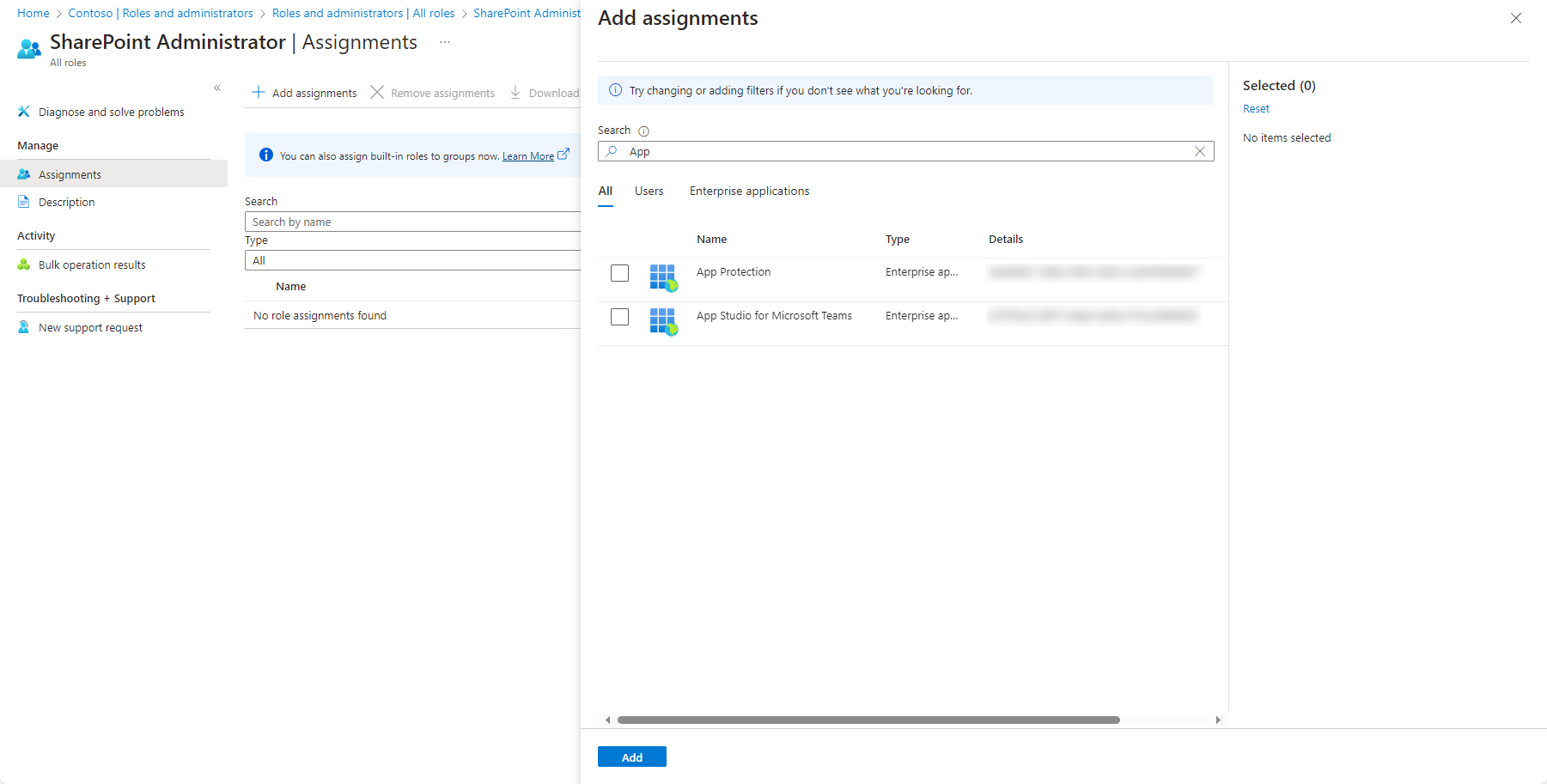
On the Assignments page, click Add assignments. The Add assignments panel appears.
-
Enter the app name in the search box to search for the app to which you want to assign the role.
-
Select the app, and click Add to assign the role. Note that the assigned role will take effect in about 30 minutes.
If your Microsoft interface is updated and different from the above screenshots, refer to the following steps to assign the SharePoint administrator role to an app:
-
Log in to Microsoft Entra admin center (or Azure portal) and navigate to Microsoft Entra ID.
-
Click Roles & admins (or Roles and administrators) in the left pane, and click SharePoint Administrator.
-
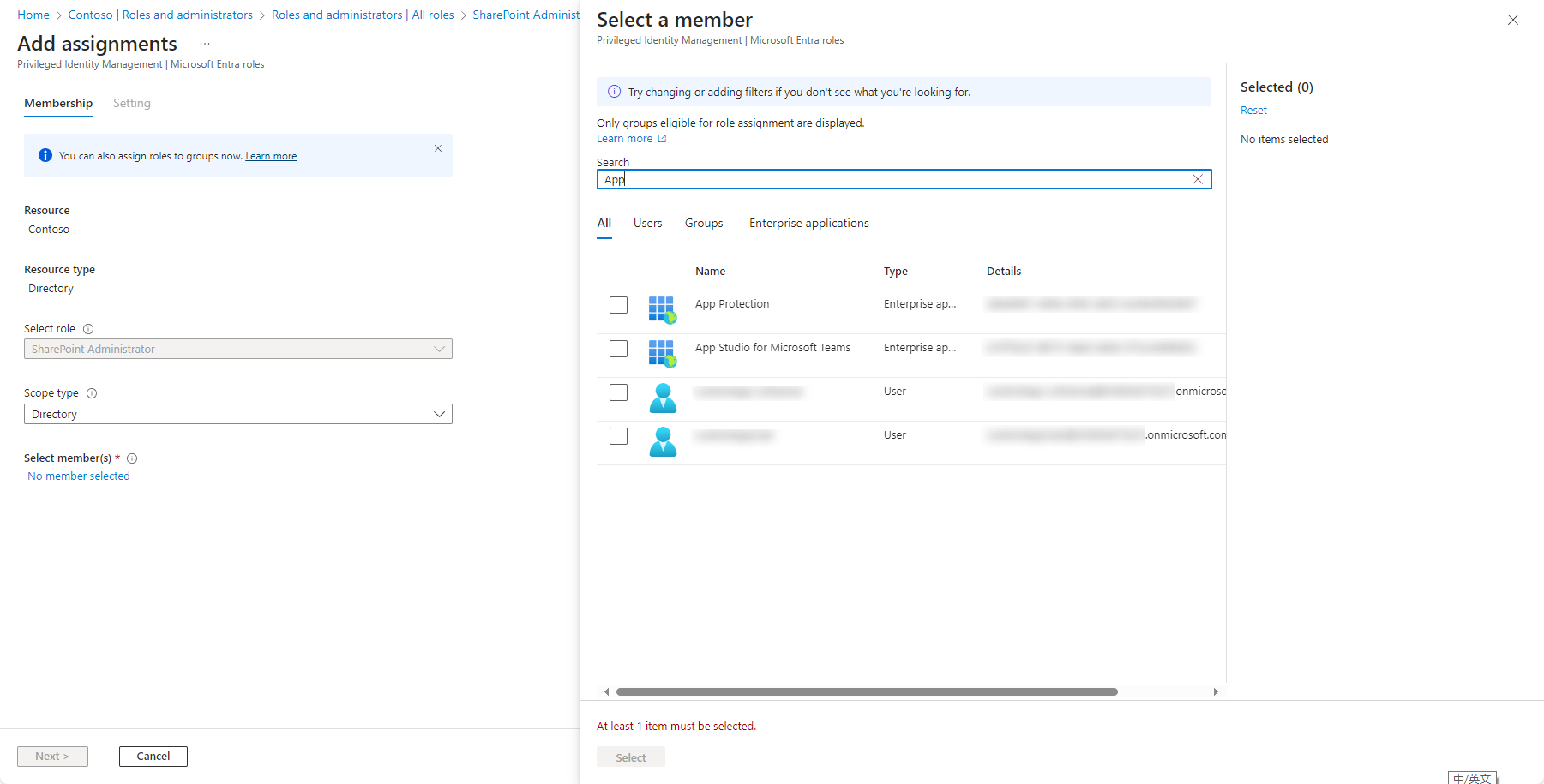
On the Assignment page, click Add assignments. The Add assignments page appears.
-
Click No member selected in the Selected member(s) section. The Select a member panel appears and enter the app name in the search box to search for the app to which you want to assign the role.
-
Click the app, and click Select to select the app.
-
Click Next.
-
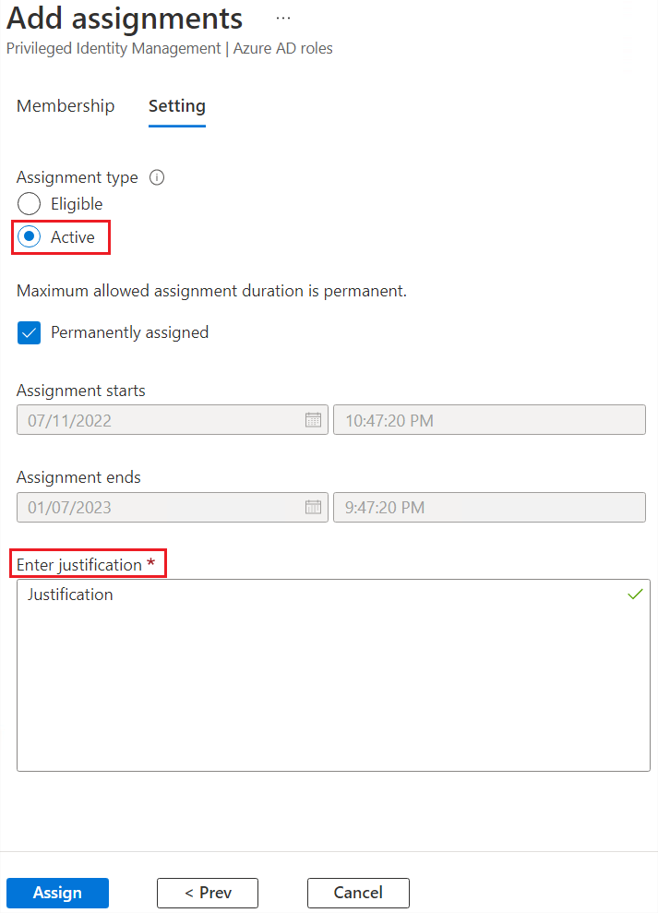
Select Active in the Assignment type section and enter the justification in the Enter justification text box.
-
Click Assign to assign the role. Note that the assigned role will take effect in about 30 minutes.
Service Account Permissions
The Tenant Owner and Service Administrators can also create a service account profile for Microsoft 365 to connect AvePoint Online Services to your Microsoft 365 tenant.
Users with Multi-Factor Authentication (MFA) enabled cannot be used as the service account to perform Aviator jobs.
If you use both the app profile and service account authentications for the destination, there are no permission requirements for the service account.
If you only use the service account authentication for the destination, make sure the service account meets the following requirements:
-
Site CollectionAdministrator
NOTEIf Fly detects that the service account is not the Site Collection Administrator, but the service account has the SharePoint Administrator or Global Administrator role, Fly will automatically add the service account as the Site Collection Administrator of the site collection.
-
SharePoint Administrator is also required in the following cases:
-
To create new site collections in the destination during the Aviator job, the destination service account must be the SharePoint Administrator.
-
To use the scan profile to scan SharePoint Online site collections in AvePoint Online Services, the service account must be the SharePoint Administrator.
NOTEIf the SharePoint Administrator cannot access the SharePoint admin center, the Global Administrator is required.
-
If the source or destination is a group site or modern site, make sure the Deny permission is removed from the source or destination site.
-
To remove the service account from the site collections, refer to the following steps:
-
Click here to download the Remove-SharePointOnlineUser.zip file. Then, extract the file.
-
In the extracted folder, configure the site collection URLs from which you want to remove the service account in the sites.csv file.
-
Install the SharePoint Online Management Shell on the Windows Server that can connect to your SharePoint Online. You can click the link to download the SharePoint Online Management Shell.
-
Open Windows PowerShell and enter the following commands in the Windows PowerShell window:
. "file path"Replace file path with the full path of the Remove-SharePointOnlineUser.ps1 file in the extracted folder, and press Enter on the keyboard.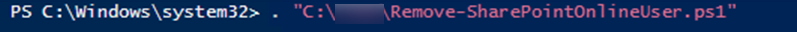
-
Enter the following commands, and press Enter on the keyboard:
Remove-SharePointOnlineUser -LoginName "" -AdministrationCenterUrl "" -Path ""-
LoginName " " – The service account you want to remove.
-
AdministrationCenterUrl " " – The SharePoint Online admin center URL.
-
Path " " – The full path of the CSV file where the site collection URLs are configured. If you want to remove the service account from all site collections in the admin center, you do not need to enter the -Path "" parameter.
-
Delegated App Profile Permissions
Fly allows you to use the Fly delegated app profile or custom delegated app profile to connect to your workspace.
Note the following:
- The license and permission requirements for the consent user are the same as those for the service account. Refer to Service Account Permissions for details.
- If the consent user of the delegated app profile has Multi-Factor Authentication (MFA) enabled, you must authorize or re-authorize the delegated app profile after MFA is enabled. Otherwise, the migration jobs using the delegated app profile will fail.
- If you re-authorize the app profile, you need to wait about one hour before using the app profile for your migration to refresh the token when there are permissions updated.
The steps of creating a default or custom delegated app profile for the destination are the same as the steps in Delegated App Profile Permissions for the source.
For Fly delegated app profile permissions, refer to the table in Fly Delegated App Profile Permissions.
For custom delegated app profile permissions, refer to the table below.
| API | Permission | Type | Purpose |
|---|---|---|---|
| Microsoft Graph | User.Read.All (Read user profiles) | Delegated | Retrieve and migrate Microsoft 365 users. |
| Microsoft Graph | RoleManagement.Read.Directory (Read directory RBAC settings) | Delegated | Retrieve and migrate Microsoft global groups. |
| Microsoft Graph | Files.Read.All (Read files in all site collections) | Delegated | Retrieve channel folders in destination team sites. |
| Microsoft Graph | Group.ReadWrite.All (Read and write all groups) | Delegated | Retrieve and migrate Microsoft 365 Groups and Group members. *Note: The permission is required in the following situations when running SharePoint Online migrations: ● Create Microsoft 365 groups and add group members when migrating source team sites related to Microsoft 365 Groups. ● Map source SharePoint Groups (Owners/Members/Visitors) to destination Microsoft 365 Groups and add users to the Microsoft 365 Groups as owners or members when migrating team sites without Microsoft 365 Groups to team sites related to Microsoft 365 Groups. If you want to use Microsoft 365 Groups Migration to migrate the Microsoft 365 Groups to which the team sites belong, you can remove this permission. |
| SharePoint | AllSites.FullControl Have full control of all site collections | Delegated | Retrieve settings and permissions of SharePoint Online site collections. |
| SharePoint | TermStore.ReadWrite.All (Read and write managed metadata) | Delegated | Retrieve and migrate to Managed Metadata Service. |
| Azure Rights Management Services For 21Vianet tenants, the API name is Microsoft Rights Management Services. | user_impersonation (Create and access protected content for users) | Delegated | Only required if you want to manage sensitivity labels of files/sites. |
| Microsoft Information Protection Sync Service | UnifiedPolicy.User.Read (Read all unified policies of the tenant) | Delegated | Only required if you want to manage sensitivity labels of files/sites. |
For easy use, you can directly use the following commands to add required API permissions through Manifest for Microsoft 365 Commercial tenants.