Home > Perform Microsoft Teams Chat Migrations > Required Permissions for Microsoft Teams Chat Migration > Destination Permissions for Google Chat Space
Download this articleDestination Permissions for Google Chat Space
To migrate to the destination Google Chat Space, the Super Admin can refer to Connect Your Tenants to AvePoint Online Services to connect your Google tenant to AvePoint Online Services at first. Then, you need to create a custom Google app profile in AvePoint Online Services > Management > App management to connect to the Google tenant.
Refer to the following section for details about how to create a custom Google app profile with required permissions.
Create a Custom Google App Profile
To use a custom Google app profile, refer to the following steps and required permissions:
-
Click Create on the App management page in AvePoint Online Services.
-
In the Select services step, select a Google tenant, and choose Fly.
-
Click Next to go to the Choose setup method step.
-
In the Choose setup method step, select the Custom mode.
-
Click Next to go to the Consent to apps step.
-
In the Consent to apps step, enter the app profile name, admin account, Google service account, and private key of your app.
-
Click Finish.
Refer to the following sections about permissions required for the custom app.
API Requirements
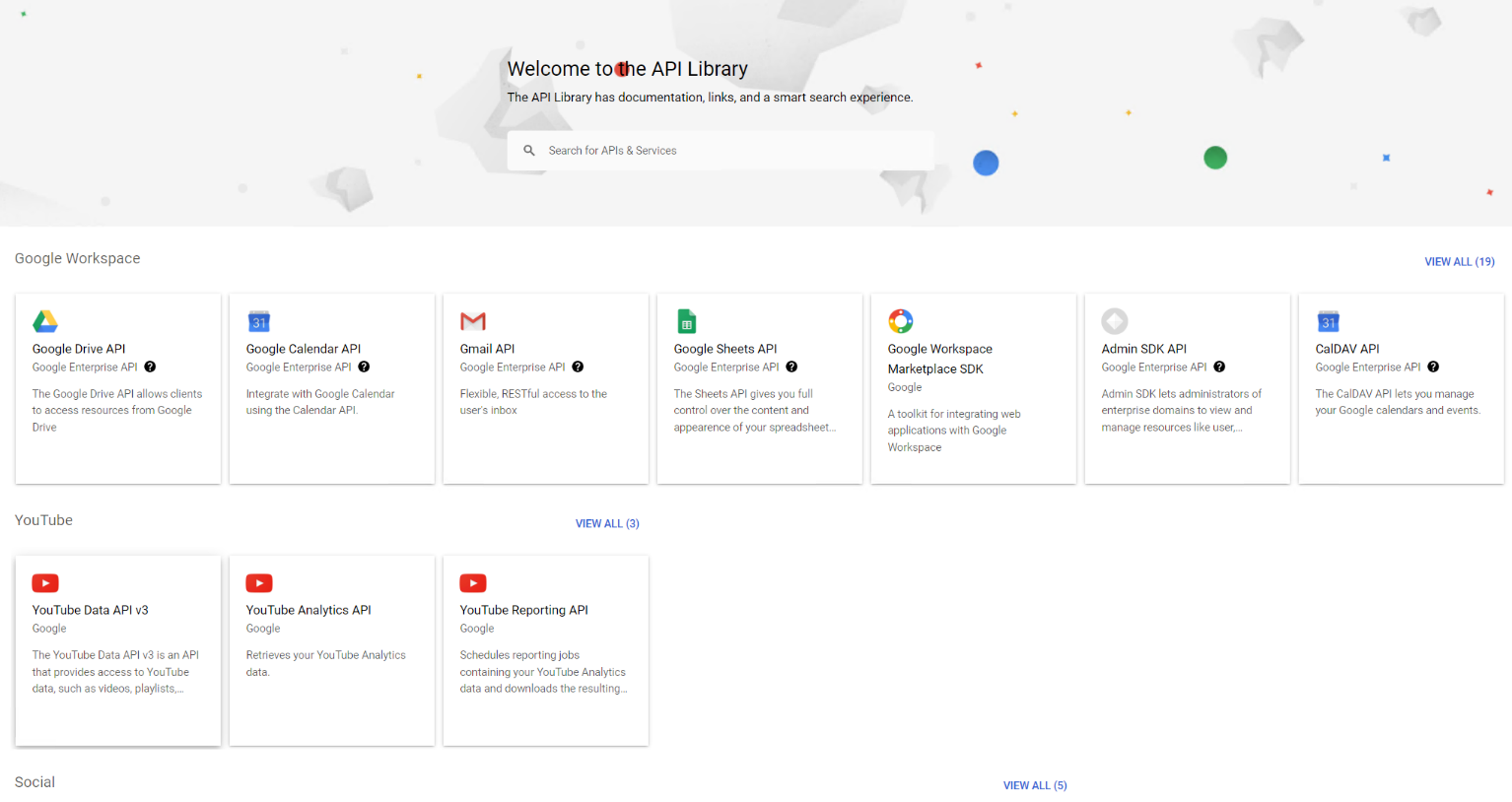
Make sure the following APIs are enabled in the projects where the service accounts are created.
-
Admin SDK API
-
Google Drive API
-
Google Chat API
-
Google Sheets API
Refer to the following steps to enable the APIs:
The user must be the project owner to enable the APIs.
-
Go to Google APIs.
-
Click ENABLE APIS AND SERVICES. The API library page appears.
-
Click the API you want to enable respectively.
-
Click ENABLE on the top of the page to enable the corresponding API.
-
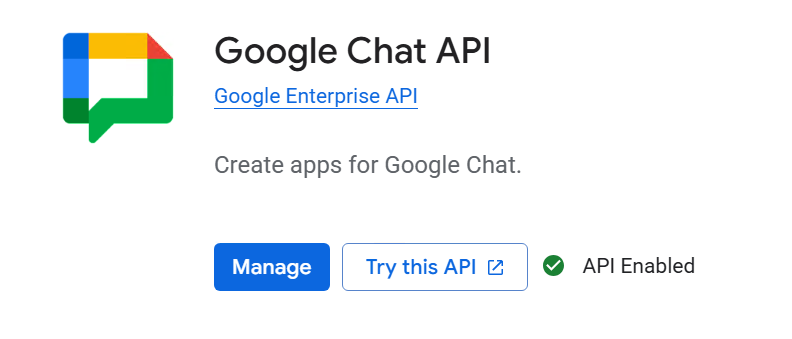
Click Google Chat API and click Manage to access the API/Service Details page.
-
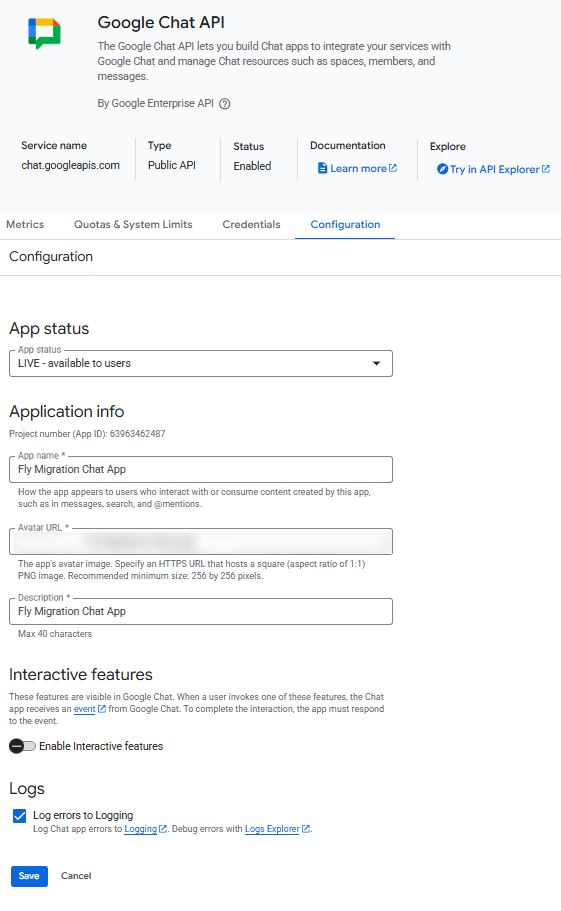
Click the CONFIGURATION tab and configure the application information.
-
App status – Select LIVE - available to users from the drop-down list.
-
App name – Enter a name for the app.
-
Avatar URL – Provide an icon for the app. Any valid URL is acceptable.
-
Description – Enter a brief description for the app.
-
Interactive features – Disable the Interactive features.
-
-
Click SAVE to save the configurations.
Make sure the API Access in your Google Workspace environment is enabled. Follow the instructions provided by Google to ensure all your settings meet the requirements.
Admin Account Permissions
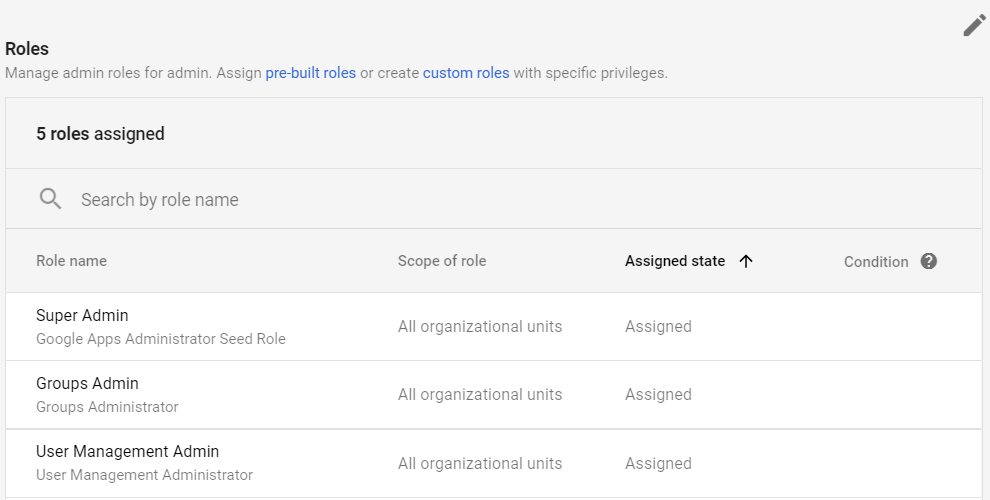
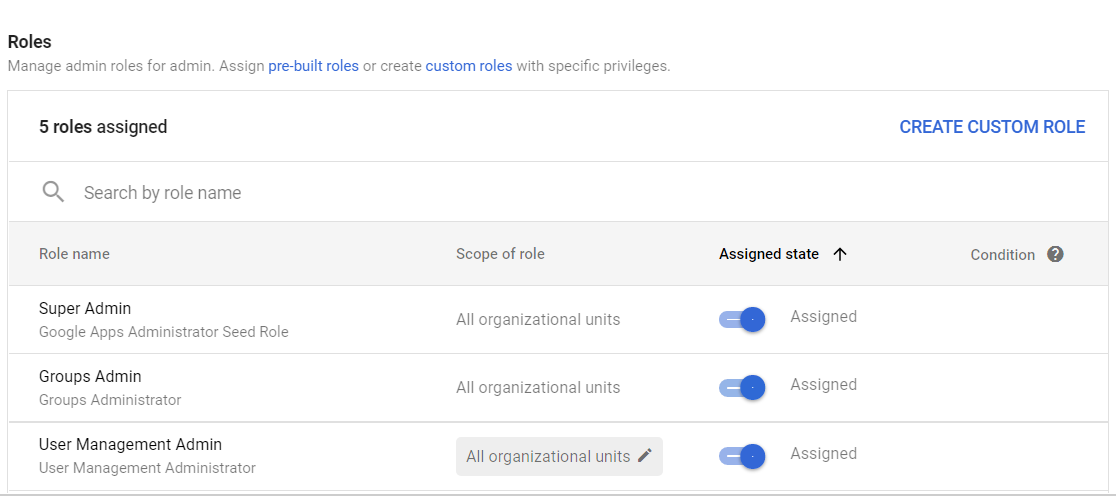
Make sure the Admin account has the following custom roles.
| Type | Admin Account Permission | Purpose |
|---|---|---|
| Google Drive | Users > Read | Migrate to user drives. |
| Google Chat | Settings (Read and Modify) | Update the properties of Google Chat spaces. |
| Google Chat | Manage chat and spaces conversation | List and manage Google Chat spaces. |
| Google Drive | Groups | Search groups for user mappings. |
To manage the roles of the Admin account, refer to the following steps:
The user must be the super administrator to manage roles.
-
Go to the Google Admin console.
-
Click Manage in the Users section.
-
Click the user you want to assign the roles. The user profile page appears.
-
Click the down arrow button in the Admin roles and privileges section.
-
Click the Pencil button in the upper-right corner of the Roles section.
-
Click CREATE CUSTOM ROLE.
-
Click Create new role.
-
Enter a name for the current role, and click CONTINUE.
-
In the Admin console privileges section, select the following privileges:
-
Google Drive
- User > Read
-
Google Chat
-
Settings (Read and Modify)
-
Manage chat and spaces conversation
-
-
Google Group
- Groups
-
-
Click CONTINUE.
-
Click CREATE ROLE. The custom role will be listed in the Roles section.
-
Click SAVE.
To allow users to access Google Drive with the Drive SDK API, refer to the following steps:
-
Go to the Google Admin console.
-
Navigate to Apps > Google Workspace > Drive and Docs.
-
Click Features and Applications.
-
Make sure the Allow users to access Google Drive with the Drive SDK API option is ON.
To allow users to access Google Chat with the Chat SDK API, refer to the following steps:
-
Go to the Google Admin console.
-
Navigate to Apps > Google Workspace > Google Chat.
-
Make sure the Service Status option is ON.
Google Service Account Permissions
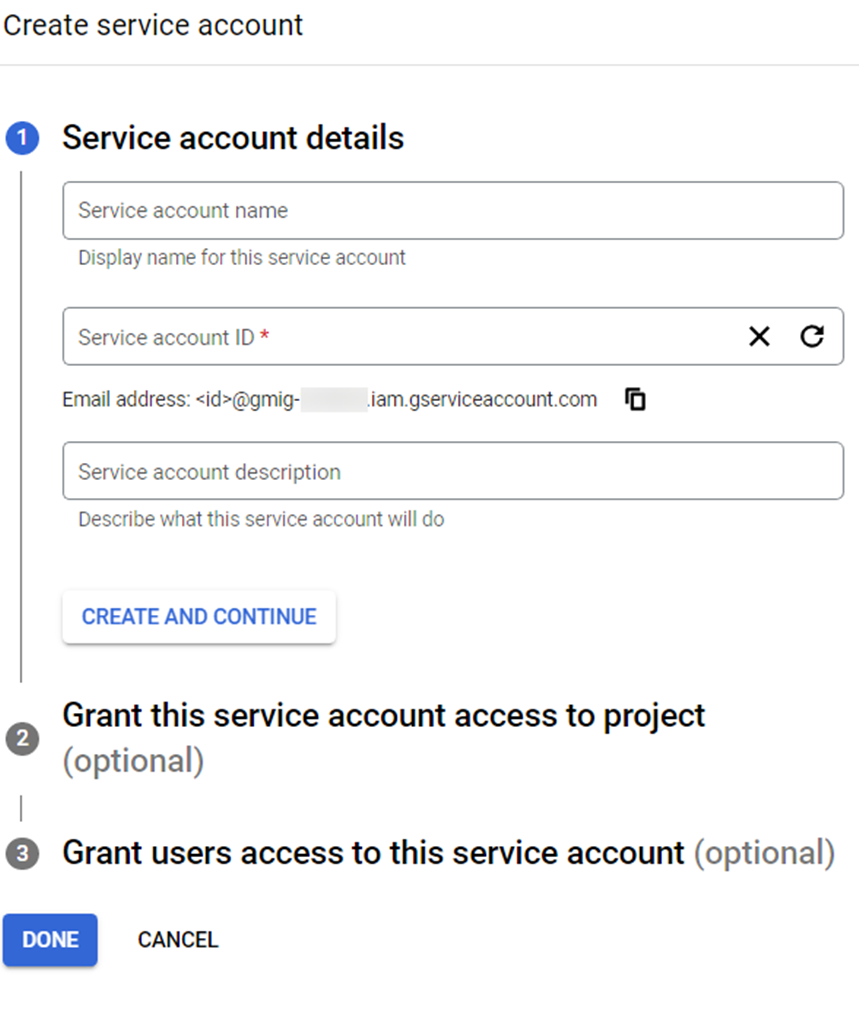
To use a Google service account, refer to the following steps:
The user must be the project owner to manage service accounts.
-
Go to the Google Service Accounts.
-
Select the desired project. The accounts in the projects are displayed.
-
To create a new service account, refer to the following steps:
NOTEIf you want to use an existing service account to add the Google Workspace connection, ignore this step.
-
Click CREATE SERVICE ACCOUNT.
-
Enter a service account name.
-
Enter the service account ID.
-
Enter the description for the service account.
-
Click CREATE AND CONTINUE. The service account is created.
-
Select the Owner role to the project from the drop-down list and click CONTINUE.
-
Click DONE.
-
-
A private key will be used when adding the connection. To obtain the private key of the service account, click the Actions button of an existing service account, click Manage keys, click ADD KEY, and then select Create new key. Select the JSON type and click CREATE to download the private key file.
NOTEIf the service account key creation is disabled in your organization, enable it first by the following steps.
-
Navigate to Google Cloud > IAM & Admin > IAM.
-
Click the resource tab and click the domain name as the resource.
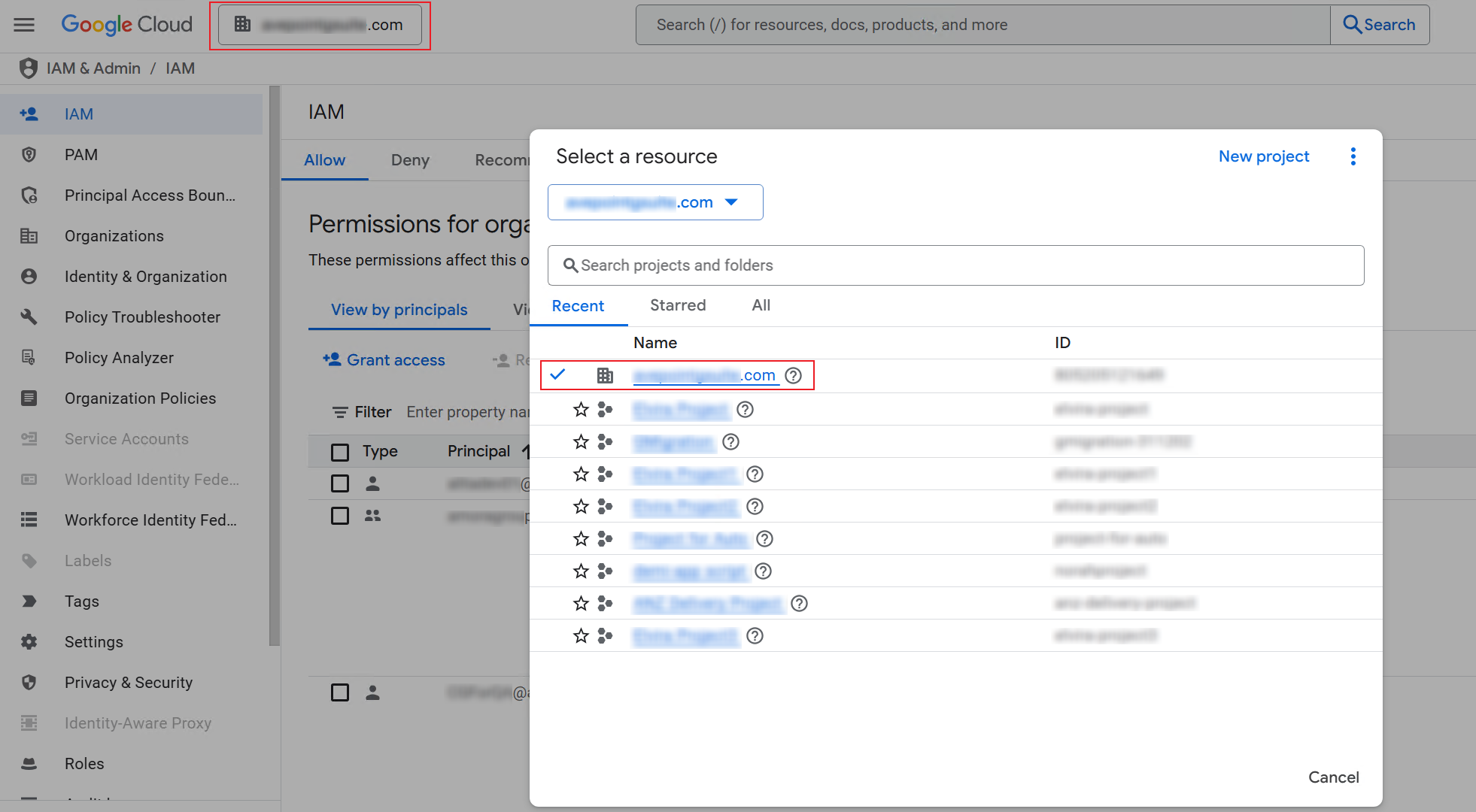
-
Click Grant access to access the Grant access to "[Tenant]" panel.
-
In the Add principals field, enter the email address of the signed-in user.
-
In the Assign roles field, select the Organization Policy Administrator role from the drop-down list.
-
Click Save to grant the role for the user to access the selected tenant.
NOTE> Make sure the current project is the project where you create the service account.
-
Click MANAGE POLICY.
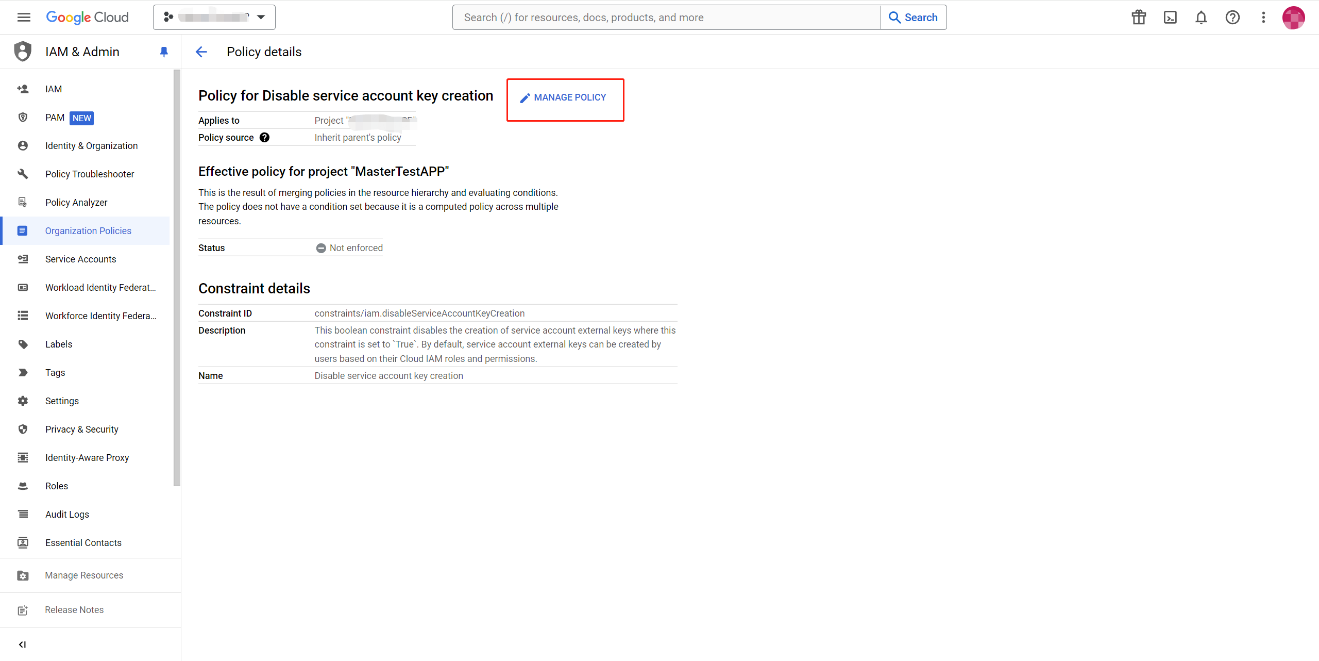
-
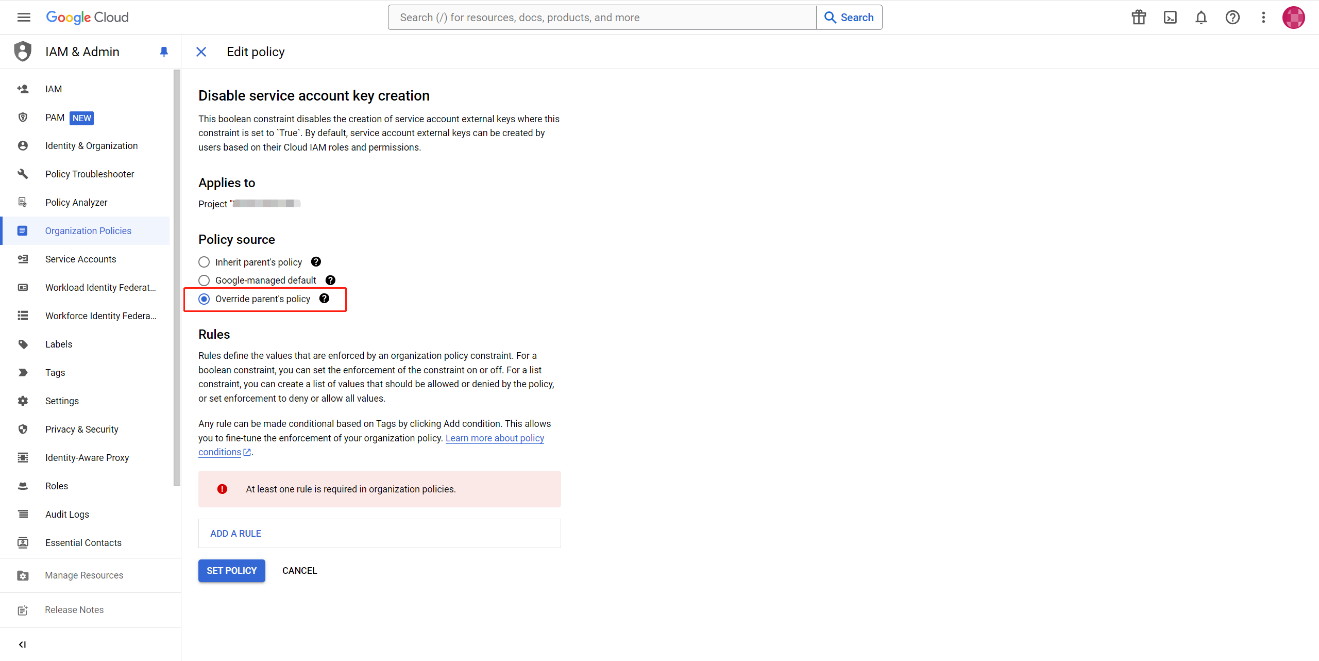
Select Override parent's policy to set a unique policy for this project.
-
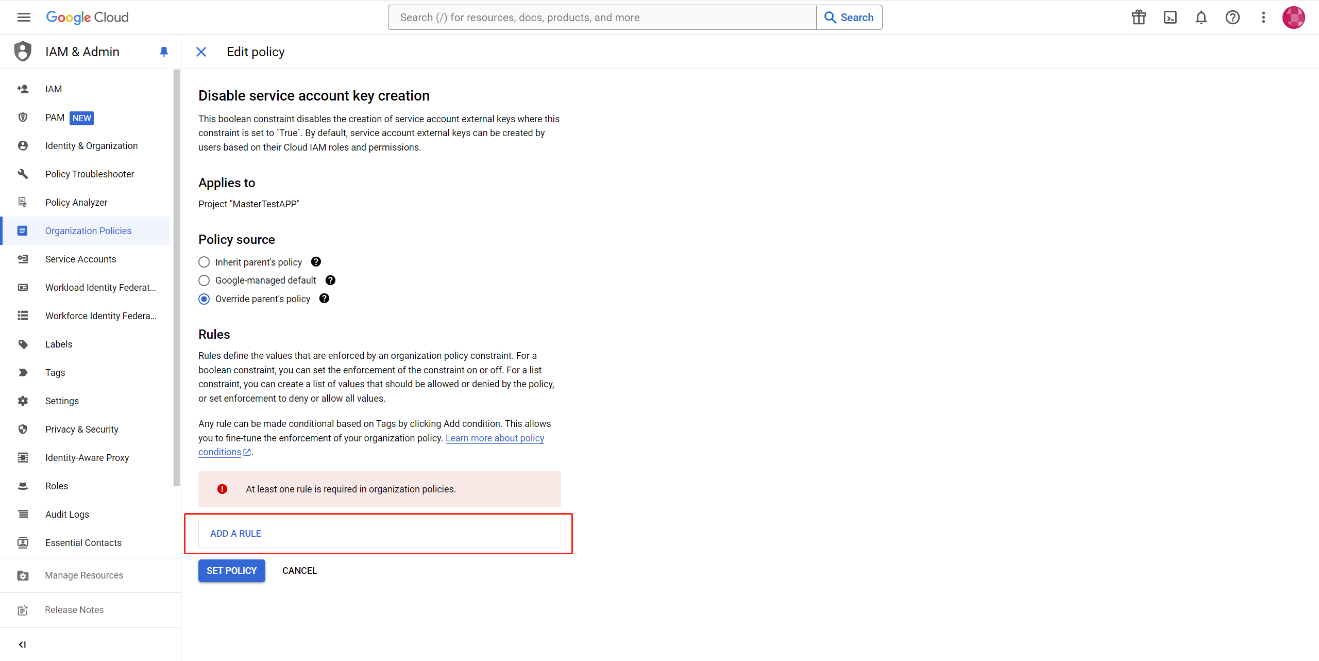
Click ADD A RULE to add a new rule.
-
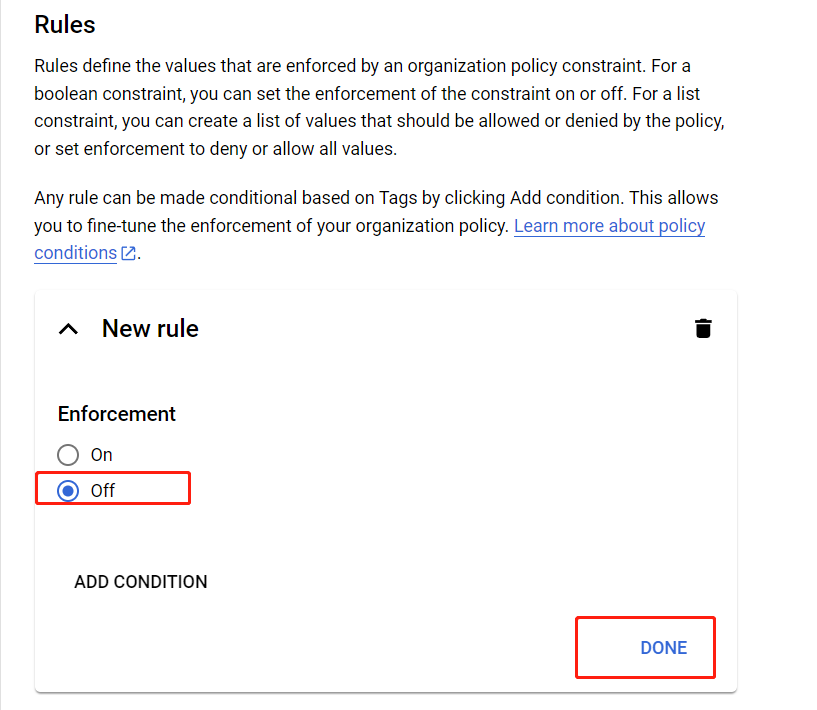
Select Off to disable the enforcement of the new rule, and click DONE.
-
Click SET POLICY.
NOTEIf you are required to have the Organization Policy Administrator role, refer to Granting Changing Revoking Access for details.
-
-
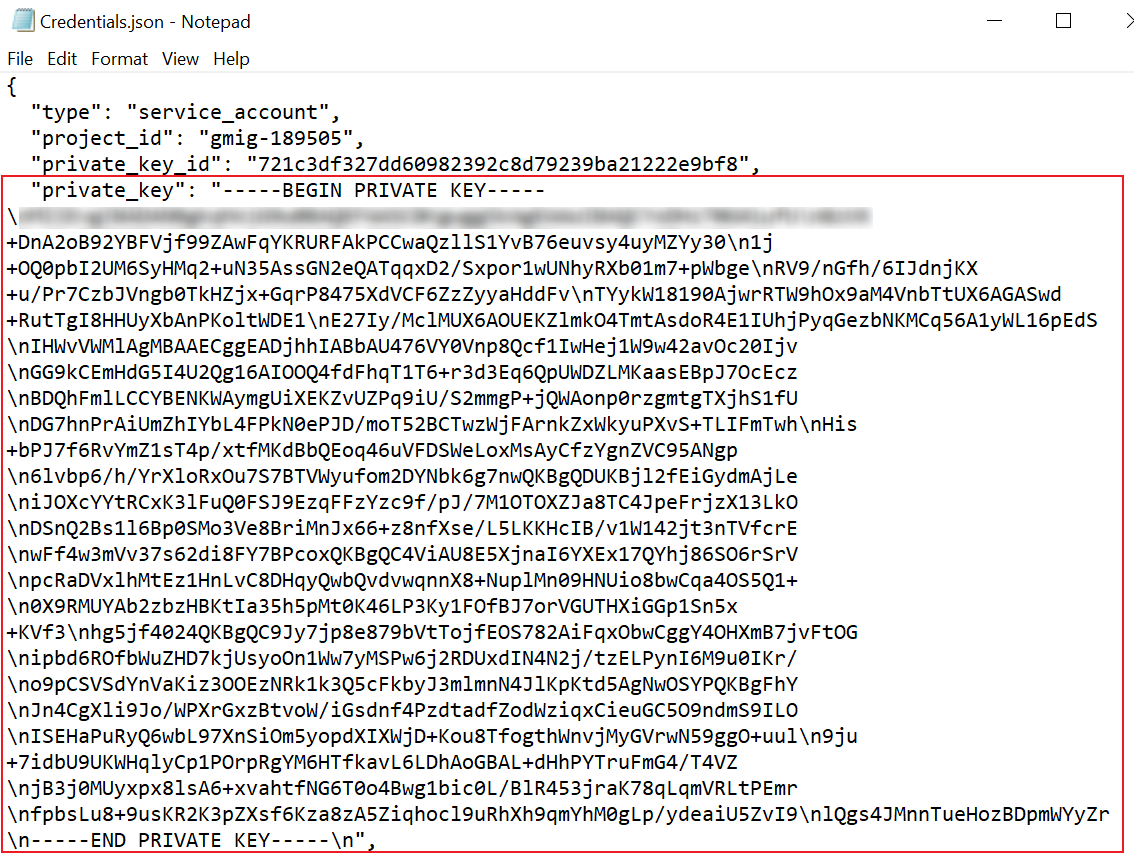
Open the .json file with Notepad and find the private key after the "private_key": node. The private key will be used when adding the connection.
-
Go to the Google Admin console using the Super administrator credentials.
-
Navigate to Security > Overview > API controls.
-
Click MANAGE DOMAIN WIDE DELEGATION.
-
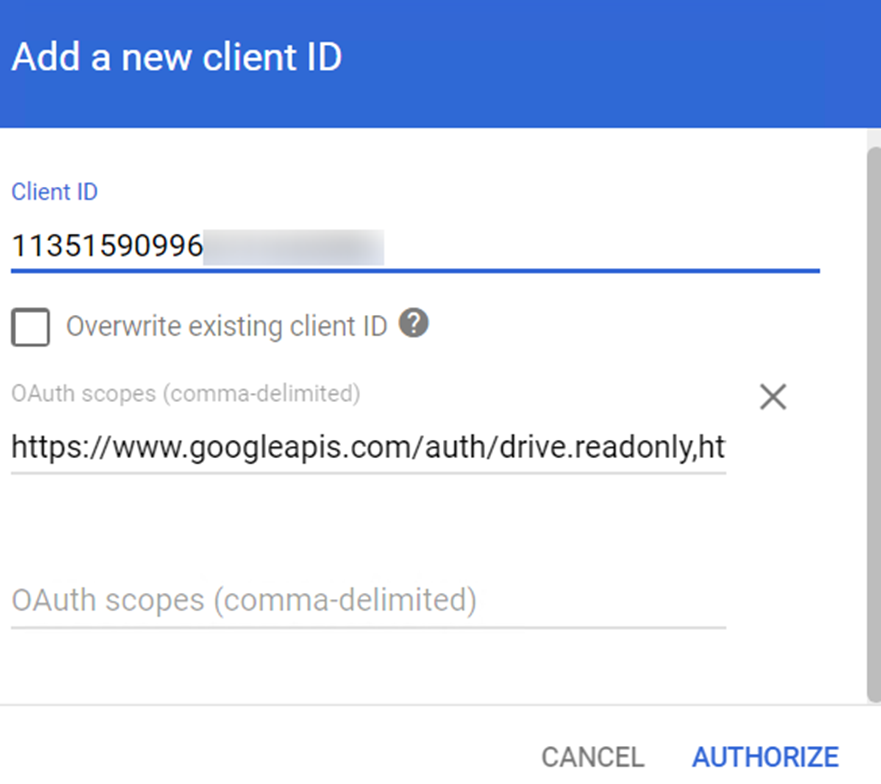
On the Domain-wide Delegation page, click Add new.
-
Enter the client ID of the service account in the Client ID field. The client ID can be found in the "client_id": " " node of the .json file in step 5.
-
Enter the following scopes in the OAuth scopes field:
https://www.googleapis.com/auth/admin.directory.user.readonly,https://www.googleapis.com/auth/admin.directory.group.readonly,https://www.googleapis.com/auth/drive,https://www.googleapis.com/auth/admin.reports.usage.readonly,https://www.googleapis.com/auth/chat.messages,https://www.googleapis.com/auth/chat.memberships,https://www.googleapis.com/auth/chat.admin.memberships.readonly,https://www.googleapis.com/auth/chat.spaces,https://www.googleapis.com/auth/chat.admin.spaces.readonly,https://www.googleapis.com/auth/chat.import,https://www.googleapis.com/auth/spreadsheets,https://www.googleapis.com/auth/admin.directory.groupThe table below lists why the scopes are needed:
Google Scopes Permission Purpose https://www.googleapis.com/auth/admin.directory.user.readonlyRetrieve destination users. https://www.googleapis.com/auth/admin.directory.group.readonlyRetrieve destination groups. https://www.googleapis.com/auth/driveMigrate folders and files. https://www.googleapis.com/auth/admin.reports.usage.readonlyRetrieve size usage of users. https://www.googleapis.com/auth/chat.messagesOperate message. https://www.googleapis.com/auth/chat.membershipsGet/add space member. https://www.googleapis.com/auth/chat.admin.memberships.readonlyGet and admin space member. https://www.googleapis.com/auth/chat.spacesGet and add space. https://www.googleapis.com/auth/chat.admin.spaces.readonlyGet and add admin space. https://www.googleapis.com/auth/chat.importImport space by import mode. https://www.googleapis.com/auth/spreadsheetsMigrate metadata to Google sheets. https://www.googleapis.com/auth/admin.directory.groupHandle Google group -
Click AUTHORIZE.