Home > App Management > Manage App Profiles for Microsoft Tenants > Configure Custom Azure App Profiles > Create a Custom Azure App
Download this articleCreate a Custom Azure App
To create a custom app, follow the steps below:
-
Go to Microsoft Entra admin center (or Microsoft Azure portal).
-
Navigate to Identity > Applications > App registrations > New registration (or Microsoft Entra ID > App registrations > New registration).
-
On the Register an application page, enter your application’s registration information:
-
Name – Enter a name for the custom application.
-
Supported account types – Select which accounts you would like this application to support.
-
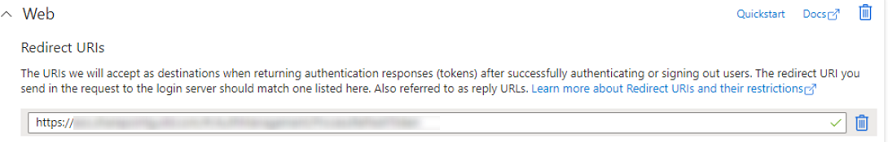
Redirect URI – This field is required when you create a custom Azure app with delegated permissions. Enter the URL of the AOS environment based on your scenario:
- Commercial production environment: https://www.avepointonlineservices.com
-
U.S. Government Production environment: https://usgov.avepointonlineservices.com
-
Insider environment: https://insider.avepointonlineservices.com
-
-
Click Register to create the custom application.
-
Click the created custom application and click API permissions.
-
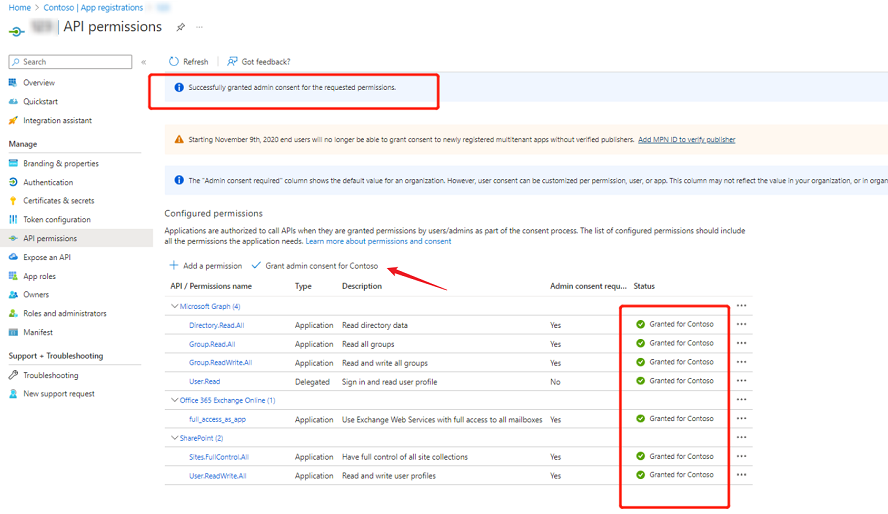
Click Add a permission to add permissions to the app.
The permissions that you need to grant to the custom app vary with the different cloud services your tenant is using. Refer to the API Permissions Required by Custom Apps section to view the required permissions for your services.
Note the following:
-
If you create a custom Azure app with delegated permissions, you also need to configure additional settings by referring to the below section: Additional Notes for Azure Apps with Delegated Permissions.
-
If you need to add permissions from Office 365 Exchange Online API, refer to Add Permissions of Office 365 Exchange Online API.
-
-
Click Grant admin consent for [Tenant name] to grant admin consent. After you have successfully granted admin consent for the requested permissions, the Status will be Granted for [Tenant name].
-
The application uses certificate authentication. Complete the following steps to upload your organization’s public certificate (.cer or .crt file types are recommended):
NOTEIf your organization does not have any certificates, you can refer to Prepare a Certificate for the Custom Azure App to prepare a self-signed certificate.
-
Locate your organization’s certificate and export the certificate as a .cer or .crt file.
-
Go to Microsoft Entra admin center (or Microsoft Azure portal), select the application, and click Certificate & secrets.
-
In the Certificates section, click Upload certificate.
-
Select the .cer or .crt file and click Add.
-
After the certificate file is successfully uploaded, it will be listed in the Certificates section.
-
Then, refer to the Consent to Custom Azure Apps section to create an app profile in the Custom mode. If necessary, you can Configure a Conditional Access Policy on Custom Apps in Azure for Best Practice.
Additional Notes for Azure Apps with Delegated Permissions
To create a custom Azure app with delegated permissions, you can refer to the instructions in the Create a Custom Azure App section above. Note that Redirect URI is required by a custom Azure app with delegated permissions, and you can refer to the following instructions to configure the setting:
-
Go to Microsoft Entra admin center (or Microsoft Azure portal).
-
Navigate to Identity > Applications > App registrations (or Microsoft Entra ID > App registrations), and then click the app that you want to configure.
-
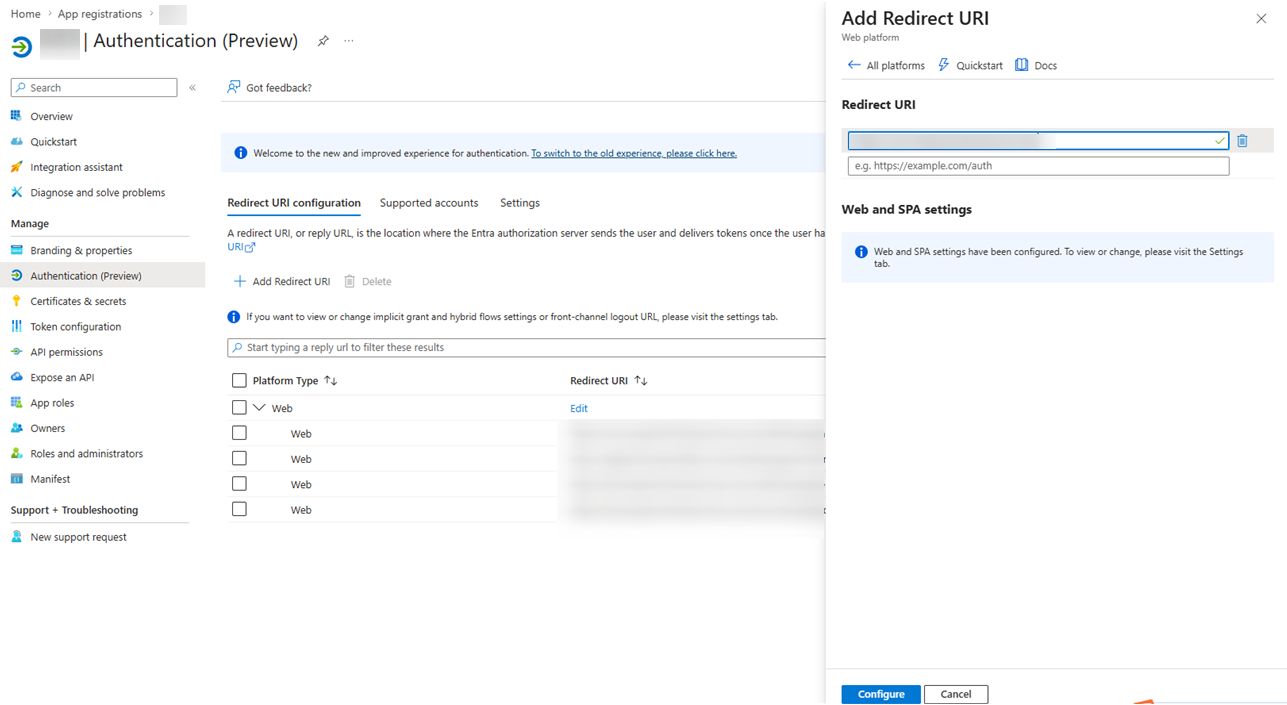
Click Authentication in the left pane.
-
On the Authentication page, click the Redirect URI configuration tab.
-
Click Add Redirect URI.
-
In the Select a platform to add redirect URI right pane, click Web.
-
In the Add Redirect URI right pane, enter a URL in the Redirect URI field based on the version of your AOS environment.
- Commercial production environment: https://www.avepointonlineservices.com
-
U.S. Government Production environment: https://usgov.avepointonlineservices.com
-
Insider environment: https://insider.avepointonlineservices.com
-
Click Configure.
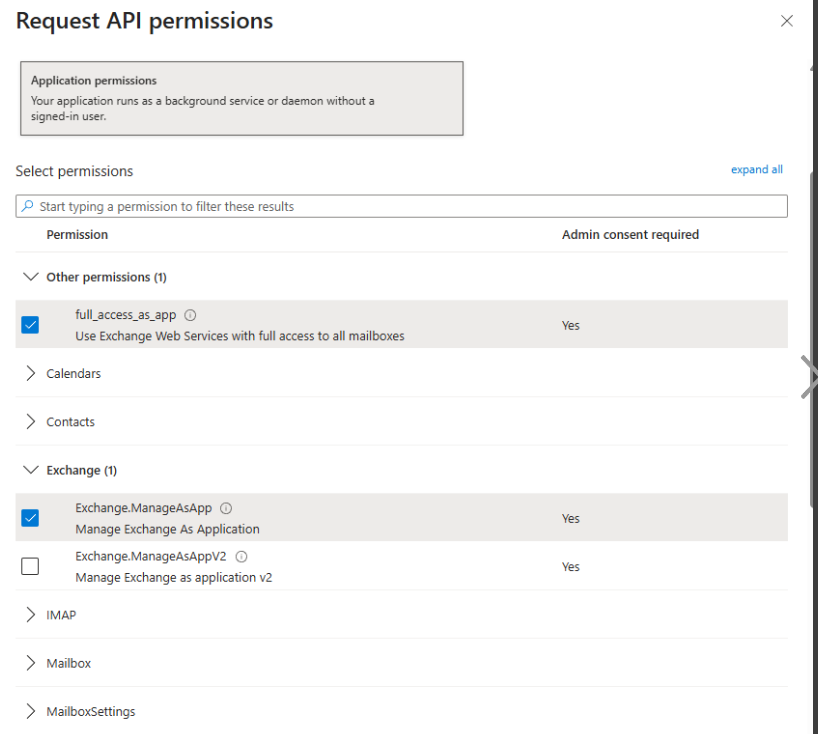
Add Permissions of Office 365 Exchange Online API
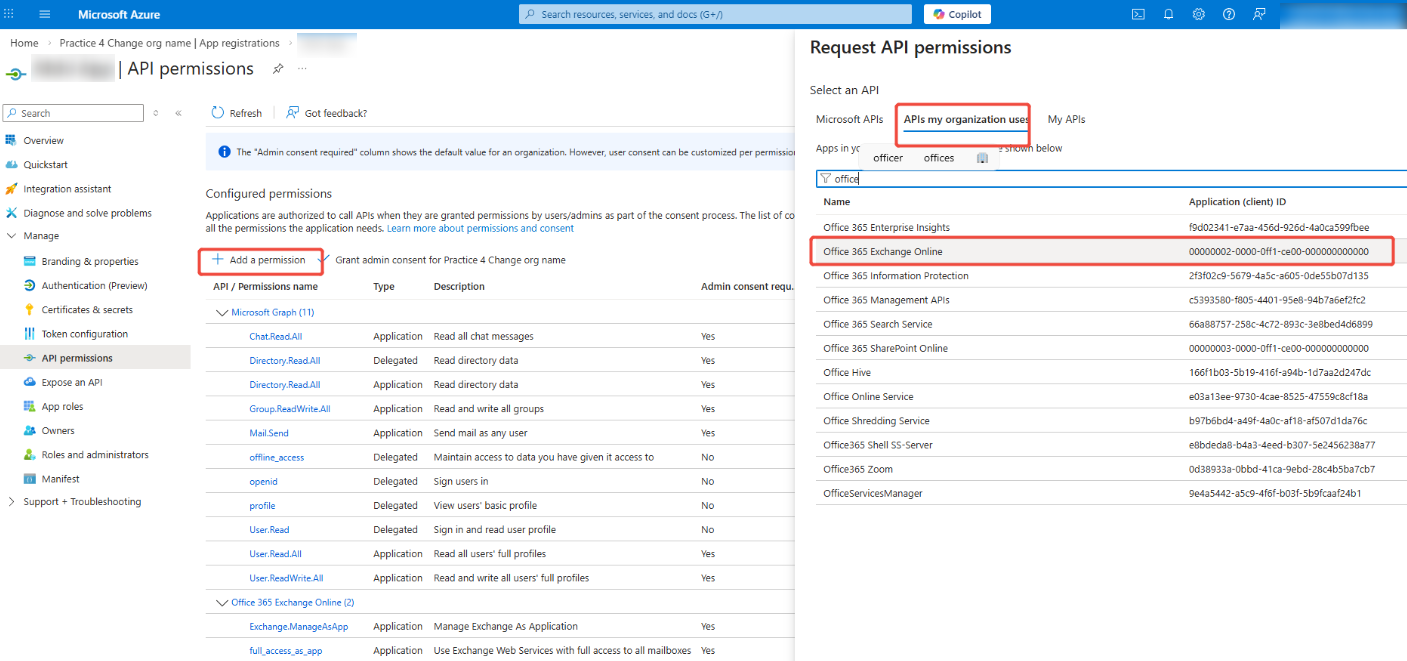
After you click Add a permission on the API permissions interface, follow the steps below to add Office 365 Exchange Online API permissions.
-
Click the APIs my organization uses tab on the Request API permissions panel.
-
Enter keywords (e.g. Office 365 Exchange Online) in the search box to search.
-
Select Office 365 Exchange Online from the displayed drop-down list.
-
Select required permissions to add to your app.
Configure a Best Practice Conditional Access Policy for Custom Apps in Azure
To ensure that custom apps in Azure are only accessible by the AvePoint Online Services production environment, follow the steps below to configure a conditional access policy.
-
Log in to Microsoft Entra admin center (or Microsoft Azure portal) and navigate to Protection (or Microsoft Entra ID > Security) > Conditional Access > Named locations.
-
Click IP ranges location.
-
In the New location (IP ranges) right pane, complete the steps below:
-
Name this location.
-
Click + to add IP ranges based on the reserved IP addresses downloaded from AvePoint Online Services. For details on the reserved IP addresses, see Download a List of Reserved IP Addresses.
-
Click Create.
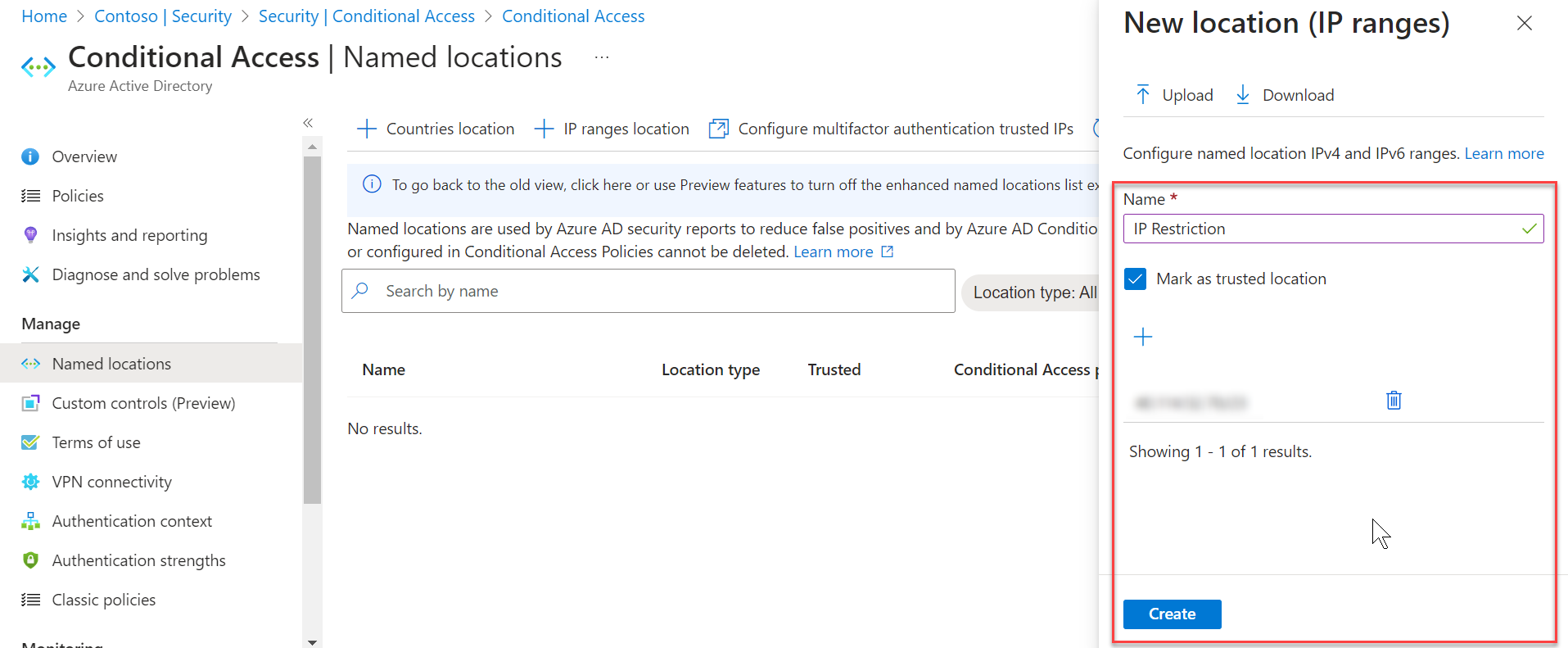
-
-
Go to the Overview page and click Create new policy.
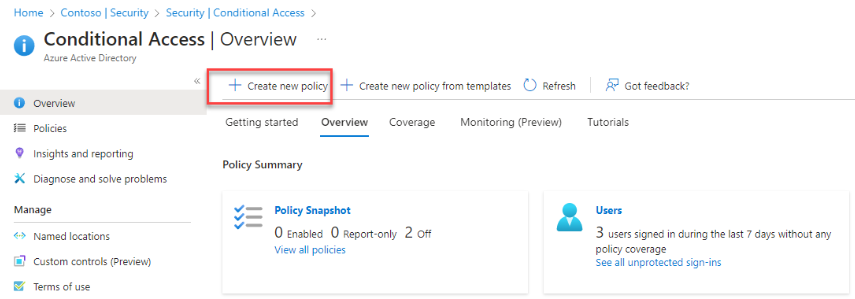
-
Refer to the following instructions to configure a new policy:
-
Enter a policy name.
-
Click Users or workload identities, select Workload identities, choose Select service principals, and select your custom apps for AvePoint cloud services.
NOTEThe Workload identities license is required for the Users or workload identities option to appear.
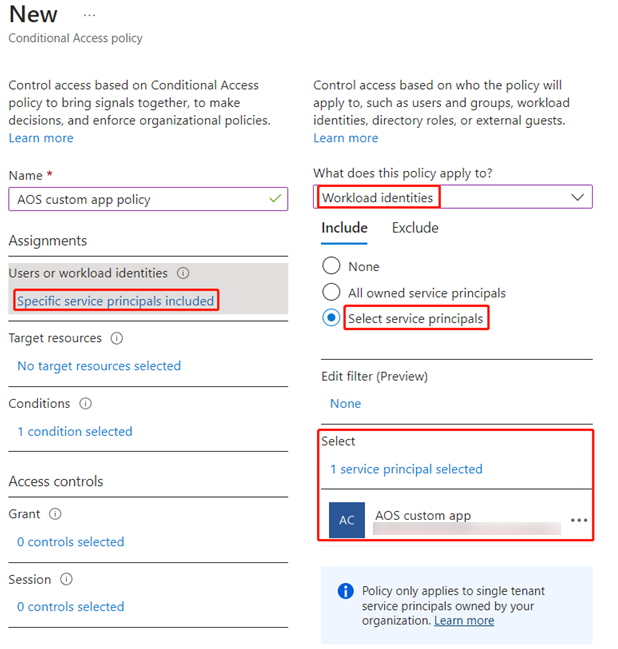
-
Click Conditions, click Locations, toggle Configure to Yes, choose the Selected locations option under the Exclude tab, and select the location created in the New location (IP ranges) step.
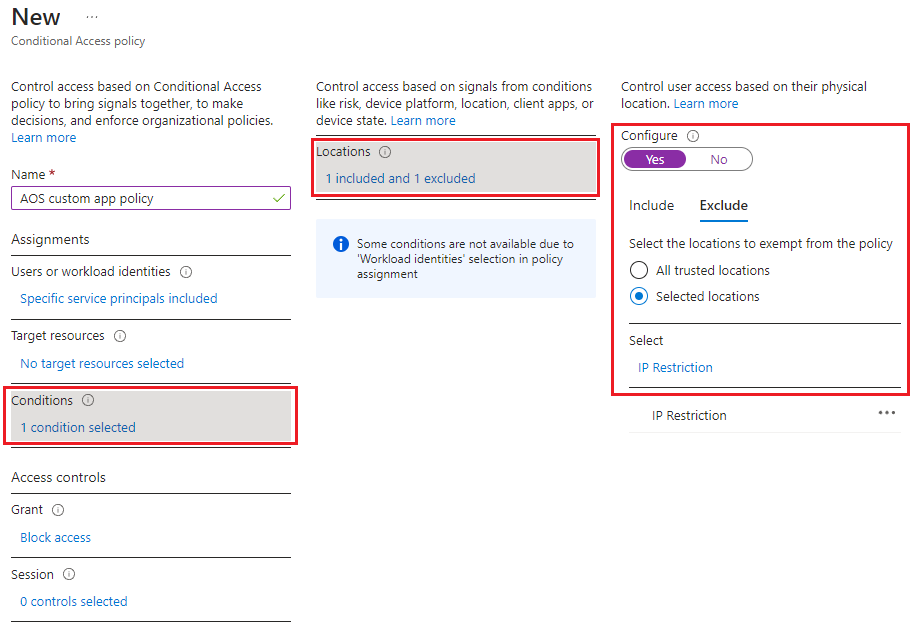
-
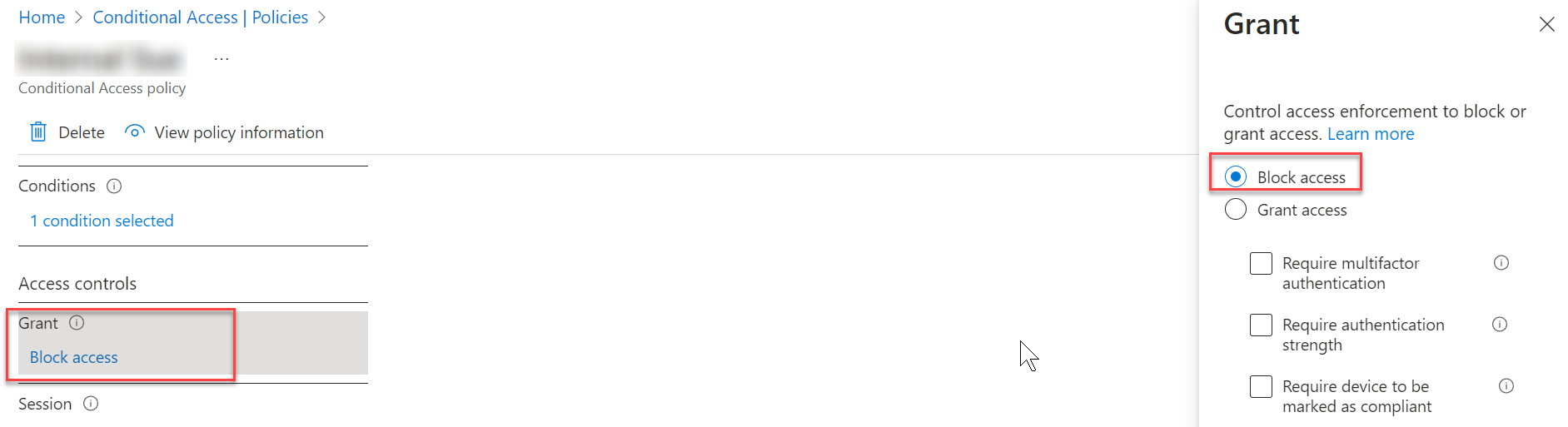
Click Grant and select Block access.
-
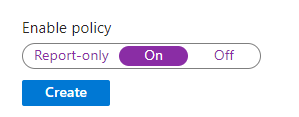
Toggle the Enable policy option to On.
-
Click Create.
-