Home > Perform Microsoft Teams Migrations > Required Permissions for Microsoft Teams Migration > Source Permissions When Destination is Teams
Export to PDFSource Permissions When Destination is Teams
To connect to the source, you can choose to only use a service account authentication, Fly app profile, or custom app profile as the authentication method. You can also use the combination of a service account authentication and a Fly app profile or the combination of a service account authentication and a custom app profile.
Refer to the following sections to view the permissions required by the authentication methods.
Fly App Profile Permissions
With the Tenant Owner or Service Administrator role, you can create a Fly app profile in AvePoint Online Services > Management > App management to connect to the Microsoft 365 tenant using the Fly app.
Refer to Fly App Profile Permissions about how to create a Fly app profile and the required permissions of the Fly app profile.
Custom App Profile Permissions
With the Tenant Owner and Service Administrator role, you can create a custom app profile in AvePoint Online Services > Management > App management to connect to the Microsoft 365 tenant using a custom Azure app.
Refer to the following procedures to create a custom app profile:
-
Prepare a certificate in Microsoft Entra ID. Refer to for more information.
You can ignore this step if you have a certificate.
-
Create a custom Azure app in Microsoft Entra ID. Refer to for more information.
-
.
-
in AvePoint Online Services.
After you re-authorize the app profile, you need to wait about one hour before using the app profile for your migration to refresh the token if there are permissions updated.
Refer to the following tables to add API permissions required by Microsoft Teams Migration to the custom Azure app.
Required by Commercial Tenants
| API | Permission | Type | Purpose |
|---|---|---|---|
| Microsoft Information Protection Sync Service | UnifiedPolicy.Tenant.Read (Read all unified policies of the tenant.) | Application | Only required if you want to manage the sensitivity labels of files/emails/Teams. |
| Microsoft Graph | Directory.Read.All (Read directory data) | Application | Only required if the source is multi-geo tenant. |
| Microsoft Graph | Domain.Read.All (Read domains) | Application | Retrieve the tenant domain. |
| Microsoft Graph | RoleManagement.Read.Directory (Read all directory RBAC settings) | Application | Retrieve directory roles. |
| Microsoft Graph | Group.Read.All (Read all groups) | Application | Retrieve Microsoft 365 Groups and Group members. |
| Microsoft Graph | Group.ReadWrite.All(Read and write all groups) | Application | Only required if you use both the app profile and the service account in the source connection and the source service account is not the team owner, to automatically add the service account as the team owner. |
| Microsoft Graph | Sites.Read.All (Read items in all site collections) | Application | Retrieve channel folders and files of team sites and private channels’ site collections. |
| Microsoft Graph | User.Read.All (Read all users’ full profiles) | Application | Retrieve information of Microsoft 365 user profiles. |
| Microsoft Graph | InformationProtectionPolicy.Read.All (Read all published labels and label policies for an organization.) | Application | Only required if you want to manage the sensitivity labels of files/emails/Teams. |
| Microsoft Graph | ChannelMember.Read.All(Read the members of all channels) | Application | Retrieve private/shared channel members. |
| Microsoft Graph | ChannelMember.ReadWrite.All(Add and remove members from all channels) | Application | Only required if you use both the app profile and the service account in the source connection and the source service account is not the private/shared channel owner, to automatically add the service account as the channel owner. |
| Microsoft Graph | ChannelMessage.Read.All(Read all channel messages) | Application | Retrieve all channel messages. |
| Microsoft Graph | TeamworkTag.Read.All(Allows the app to read tags in Teams without a signed-in user) | Application | Retrieve tags. |
| Microsoft Graph | TeamMember.Read.All(Read the members of all teams) | Application | Retrieve Team members. |
| Microsoft Graph | TeamSettings.Read.All(Read all teams’ settings) | Application | Retrieve and migrate Team settings. |
| Microsoft Graph | ChannelSettings.Read.All(Read the names, descriptions, and settings of all channels) | Application | Retrieve and migrate channel settings. |
| Microsoft Graph | TeamsAppInstallation.ReadForTeam.All(Read installed Teams apps for all teams) | Application | Retrieve and migrate Team apps. |
| Microsoft Graph | TeamsTab.Read.All(Read tabs in Microsoft Teams) | Application | Retrieve and migrate Team tabs. |
| Microsoft Graph | Schedule.Read.All(Read all schedule items) | Application | Retrieve and migrate Teams Shifts app data. |
| Microsoft Graph | Reports.Read.All(Read all usage reports) | Application | Only required by tenant discovery. |
| Microsoft Graph | ReportSettings.Read.All(Read all admin report settings) | Application | Retrieve the Reports setting of the Microsoft 365 admin center. |
| Microsoft Graph | Tasks.Read.All(Read all users’ tasks and tasklist) | Application | Retrieve planners and data in planners. |
| Azure Rights Management Services | Content.SuperUser (Read all protected content for this tenant) | Application | Only required if you want to manage the sensitivity labels of files/emails/Teams. |
| Office 365 Exchange Online | Exchange.ManageAsApp (Manage Exchange As Application) | Application | Use Exchange PowerShell to retrieve mailbox permissions. |
| Office 365 Exchange Online | Full_access_as_app (Use Exchange Web Services with full access to all mailboxes) | Application | Retrieve items from all mailboxes. *Note: If you do not want to add this permission to the app, you can create an RBAC assignment for the app to only access to specified mailboxes. Refer to the option 3 in the How to Migrate Mailboxes without the ApplicationImpersonation Role? section for details. |
| SharePoint/Office 365 SharePoint Online | Sites.FullControl.All (Have full control of all site collections) | Application | Retrieve settings and permissions of team sites. |
| SharePoint/Office 365 SharePoint Online | TermStore.ReadWrite.All (Read and write managed metadata) | Application | Retrieve and migrate Managed Metadata Service.*Note: The TermStore.ReadWrite.All permission is required to migrate the term set used in the Managed Navigation. If you do not need to migrate the term set used in the Managed Navigation, you can replace the permission with TermStore.Read.All. |
For easy use, you can directly use the following commands to add required API permissions through Manifest.
"requiredResourceAccess": [
{
"resourceAppId": "00000003-0000-0000-c000-000000000000",
"resourceAccess": [
{
"id": "3b55498e-47ec-484f-8136-9013221c06a9",
"type": "Role"
},
{
"id": "35930dcf-aceb-4bd1-b99a-8ffed403c974",
"type": "Role"
},
{
"id": "7b2449af-6ccd-4f4d-9f78-e550c193f0d1",
"type": "Role"
},
{
"id": "c97b873f-f59f-49aa-8a0e-52b32d762124",
"type": "Role"
},
{
"id": "7ab1d382-f21e-4acd-a863-ba3e13f7da61",
"type": "Role"
},
{
"id": "dbb9058a-0e50-45d7-ae91-66909b5d4664",
"type": "Role"
},
{
"id": "5b567255-7703-4780-807c-7be8301ae99b",
"type": "Role"
},
{
"id": "62a82d76-70ea-41e2-9197-370581804d09",
"type": "Role"
},
{
"id": "19da66cb-0fb0-4390-b071-ebc76a349482",
"type": "Role"
},
{
"id": "230c1aed-a721-4c5d-9cb4-a90514e508ef",
"type": "Role"
},
{
"id": "ee353f83-55ef-4b78-82da-555bfa2b4b95",
"type": "Role"
},
{
"id": "483bed4a-2ad3-4361-a73b-c83ccdbdc53c",
"type": "Role"
},
{
"id": "7b2ebf90-d836-437f-b90d-7b62722c4456",
"type": "Role"
},
{
"id": "332a536c-c7ef-4017-ab91-336970924f0d",
"type": "Role"
},
{
"id": "f10e1f91-74ed-437f-a6fd-d6ae88e26c1f",
"type": "Role"
},
{
"id": "660b7406-55f1-41ca-a0ed-0b035e182f3e",
"type": "Role"
},
{
"id": "1f615aea-6bf9-4b05-84bd-46388e138537",
"type": "Role"
},
{
"id": "242607bd-1d2c-432c-82eb-bdb27baa23ab",
"type": "Role"
},
{
"id": "46890524-499a-4bb2-ad64-1476b4f3e1cf",
"type": "Role"
},
{
"id": "b74fd6c4-4bde-488e-9695-eeb100e4907f",
"type": "Role"
},
{
"id": "df021288-bdef-4463-88db-98f22de89214",
"type": "Role"
}
]
},
{
"resourceAppId": "00000003-0000-0ff1-ce00-000000000000",
"resourceAccess": [
{
"id": "c8e3537c-ec53-43b9-bed3-b2bd3617ae97",
"type": "Role"
},
{
"id": "678536fe-1083-478a-9c59-b99265e6b0d3",
"type": "Role"
}
]
},
{
"resourceAppId": "00000002-0000-0ff1-ce00-000000000000",
"resourceAccess": [
{
"id": "dc890d15-9560-4a4c-9b7f-a736ec74ec40",
"type": "Role"
},
{
"id": "dc50a0fb-09a3-484d-be87-e023b12c6440",
"type": "Role"
}
]
},
{
"resourceAppId": "870c4f2e-85b6-4d43-bdda-6ed9a579b725",
"resourceAccess": [
{
"id": "8b2071cd-015a-4025-8052-1c0dba2d3f64",
"type": "Role"
}
]
},
{
"resourceAppId": "00000012-0000-0000-c000-000000000000",
"resourceAccess": [
{
"id": "7347eb49-7a1a-43c5-8eac-a5cd1d1c7cf0",
"type": "Role"
}
]
}
],
Required by GCC High Tenants
| API | Permission | Type | Purpose |
|---|---|---|---|
| Microsoft Information Protection Sync Service | UnifiedPolicy.Tenant.Read (Read all unified policies of the tenant.) | Application | Only required if you want to manage the sensitivity labels of files/emails/Teams. |
| Microsoft Graph | Domain.Read.All(Read domains) | Application | Retrieve the tenant domain. |
| Microsoft Graph | RoleManagement.Read.Directory(Read all directory RBAC settings) | Application | Retrieve directory roles. |
| Microsoft Graph | Group.Read.All (Read all groups) | Application | Retrieve Microsoft 365 Groups and Group members. |
| Microsoft Graph | Group.ReadWrite.All(Read and write all groups) | Application | Only required if you use both the app profile and the service account in the source connection and the source service account is not the Team owner, to automatically add the service account as the Team owner. |
| Microsoft Graph | Sites.Read.All (Read items in all site collections) | Application | Retrieve channel folders and files of team sites and private channels’ site collections. |
| Microsoft Graph | User.Read.All (Read all users’ full profiles) | Application | Retrieve information of Microsoft 365 user profiles. |
| Microsoft Graph | InformationProtectionPolicy.Read.All (Read all published labels and label policies for an organization.) | Application | Only required if you want to manage the sensitivity labels of files/emails/Teams. |
| Microsoft Graph | ChannelMember.Read.All(Read the members of all channels) | Application | Retrieve private/shared channel members. |
| Microsoft Graph | ChannelMember.ReadWrite.All(Add and remove members from all channels) | Application | Only required if you use both the app profile and the service account in the source connection and the source service account is not the private/shared channel owner, to automatically add the service account as the channel owner. |
| Microsoft Graph | ChannelMessage.Read.All(Read all channel messages) | Application | Retrieve all channel messages. |
| Microsoft Graph | TeamMember.Read.All(Read the members of all teams) | Application | Retrieve Team members. |
| Microsoft Graph | TeamSettings.Read.All(Read all teams’ settings) | Application | Retrieve and migrate Team settings. |
| Microsoft Graph | ChannelSettings.Read.All(Read the names, descriptions, and settings of all channels) | Application | Retrieve and migrate channel settings. |
| Microsoft Graph | TeamsAppInstallation.ReadForTeam.All(Read installed Teams apps for all teams) | Application | Retrieve and migrate Team apps. |
| Microsoft Graph | TeamsTab.Read.All(Read tabs in Microsoft Teams) | Application | Retrieve and migrate Team tabs. |
| Microsoft Graph | Reports.Read.All(Read all usage reports) | Application | Only required by tenant discovery. |
| Microsoft Graph | ReportSettings.Read.All(Read all admin report settings) | Application | Retrieve the Reports setting of the Microsoft 365 admin center. |
| Microsoft Graph | Tasks.Read.All(Read all users’ tasks and tasklist) | Application | Retrieve planners and data in planners. |
| Microsoft Graph | TeamworkTag.Read.All(Allows the app to read tags in Teams without a signed-in user) | Application | Retrieve tags. |
| Azure Rights Management Services | Content.SuperUser (Read all protected content for this tenant) | Application | Only required if you want to manage the sensitivity labels of files/emails/Teams. |
| Office 365 Exchange Online | Exchange.ManageAsApp (Manage Exchange As Application) | Application | Use Exchange PowerShell to retrieve mailbox permissions. |
| Office 365 Exchange Online | Full_access_as_app (Use Exchange Web Services with full access to all mailboxes) | Application | Retrieve items from all mailboxes. *Note: If you do not want to add this permission to the app, you can create an RBAC assignment for the app to only access to specified mailboxes. Refer to the option 3 in the How to Migrate Mailboxes without the ApplicationImpersonation Role? section for details. |
| SharePoint/Office 365 SharePoint Online | Sites.FullControl.All (Have full control of all site collections) | Application | Retrieve settings and permissions of team sites. |
| SharePoint/Office 365 SharePoint Online | TermStore.ReadWrite.All (Read and write managed metadata) | Application | Retrieve and migrate Managed Metadata Service.*Note: The TermStore.ReadWrite.All permission is required to migrate the term set used in the Managed Navigation. If you do not need to migrate the term set used in the Managed Navigation, you can replace the permission with TermStore.Read.All. |
For easy use, you can directly use the following commands to add required API permissions through Manifest.
"requiredResourceAccess": [
{
"resourceAppId": "00000003-0000-0000-c000-000000000000",
"resourceAccess": [
{
"id": " b74fd6c4-4bde-488e-9695-eeb100e4907f",
"type": "Role"
},
{
"id": "3b55498e-47ec-484f-8136-9013221c06a9",
"type": "Role"
},
{
"id": "35930dcf-aceb-4bd1-b99a-8ffed403c974",
"type": "Role"
},
{
"id": "7b2449af-6ccd-4f4d-9f78-e550c193f0d1",
"type": "Role"
},
{
"id": "c97b873f-f59f-49aa-8a0e-52b32d762124",
"type": "Role"
},
{
"id": "dbb9058a-0e50-45d7-ae91-66909b5d4664",
"type": "Role"
},
{
"id": "5b567255-7703-4780-807c-7be8301ae99b",
"type": "Role"
},
{
"id": "62a82d76-70ea-41e2-9197-370581804d09",
"type": "Role"
},
{
"id": "19da66cb-0fb0-4390-b071-ebc76a349482",
"type": "Role"
},
{
"id": "230c1aed-a721-4c5d-9cb4-a90514e508ef",
"type": "Role"
},
{
"id": "925396cc-885d-40f4-89e6-450b1f192955",
"type": "Role"
},
{
"id": "483bed4a-2ad3-4361-a73b-c83ccdbdc53c",
"type": "Role"
},
{
"id": "332a536c-c7ef-4017-ab91-336970924f0d",
"type": "Role"
},
{
"id": "c0bf4420-ed41-4c4e-8ce8-d96bfc03f7d7",
"type": "Role"
},
{
"id": "660b7406-55f1-41ca-a0ed-0b035e182f3e",
"type": "Role"
},
{
"id": "1f615aea-6bf9-4b05-84bd-46388e138537",
"type": "Role"
},
{
"id": "242607bd-1d2c-432c-82eb-bdb27baa23ab",
"type": "Role"
},
{
"id": "46890524-499a-4bb2-ad64-1476b4f3e1cf",
"type": "Role"
},
{
"id": "df021288-bdef-4463-88db-98f22de89214",
"type": "Role"
}
]
},
{
"resourceAppId": "00000012-0000-0000-c000-000000000000",
"resourceAccess": [
{
"id": "7347eb49-7a1a-43c5-8eac-a5cd1d1c7cf0",
"type": "Role"
}
]
},
{
"resourceAppId": "870c4f2e-85b6-4d43-bdda-6ed9a579b725",
"resourceAccess": [
{
"id": "8b2071cd-015a-4025-8052-1c0dba2d3f64",
"type": "Role"
}
]
},
{
"resourceAppId": "00000002-0000-0ff1-ce00-000000000000",
"resourceAccess": [
{
"id": "dc890d15-9560-4a4c-9b7f-a736ec74ec40",
"type": "Role"
},
{
"id": "dc50a0fb-09a3-484d-be87-e023b12c6440",
"type": "Role"
}
]
},
{
"resourceAppId": "00000003-0000-0ff1-ce00-000000000000",
"resourceAccess": [
{
"id": "c8e3537c-ec53-43b9-bed3-b2bd3617ae97",
"type": "Role"
},
{
"id": "678536fe-1083-478a-9c59-b99265e6b0d3",
"type": "Role"
}
]
}
],
Required by 21Vianet Tenants
| API | Permission | Type | Purpose |
|---|---|---|---|
| Microsoft Graph | Domain.Read.All (Read domains) | Application | Retrieve the tenant domain. |
| Microsoft Graph | RoleManagement.Read.Directory (Read all directory RBAC settings) | Application | Retrieve directory roles. |
| Microsoft Graph | Group.Read.All (Read all groups) | Application | Retrieve Microsoft 365 Groups and Group members. |
| Microsoft Graph | Group.ReadWrite.All(Read and write all groups) | Application | Only required if you use both the app profile and the service account in the source connection and the source service account is not the Team owner, to automatically add the service account as the Team owner. |
| Microsoft Graph | Sites.ReadWrite.All (Read items in all site collections) | Application | Retrieve channel folders and files of team sites and private channels’ site collections. |
| Microsoft Graph | User.Read.All (Read all users’ full profiles) | Application | Retrieve information of Microsoft 365 user profiles. |
| Microsoft Graph | ChannelMember.Read.All(Read the members of all channels) | Application | Retrieve private/shared channel members. |
| Microsoft Graph | ChannelMember.ReadWrite.All(Add and remove members from all channels) | Application | Only required if you use both the app profile and the service account in the source connection and the source service account is not the private/shared channel owner, to automatically add the service account as the channel owner. |
| Microsoft Graph | ChannelMessage.Read.All(Read all channel messages) | Application | Retrieve all channel messages. |
| Microsoft Graph | TeamworkTag.Read.All(Allows the app to read tags in Teams without a signed-in user) | Application | Retrieve tags. |
| Microsoft Graph | TeamMember.Read.All(Read the members of all teams) | Application | Retrieve Team members. |
| Microsoft Graph | TeamSettings.Read.All(Read all teams’ settings) | Application | Retrieve and migrate Team settings. |
| Microsoft Graph | TeamsAppInstallation.ReadForTeam.All(Read installed Teams apps for all teams) | Application | Retrieve and migrate Team apps. |
| Microsoft Graph | TeamsTab.Read.All(Read tabs in Microsoft Teams) | Application | Retrieve and migrate Team tabs. |
| Office 365 Exchange Online | Exchange.ManageAsApp(Manage Exchange As Application) | Application | Use Exchange PowerShell to retrieve mailbox permissions. |
| Office 365 Exchange Online | Full_access_as_app(Use Exchange Web Services with full access to all mailboxes) | Application | Retrieve items from all mailboxes. *Note: If you do not want to add this permission to the app, you can create an RBAC assignment for the app to only access to specified mailboxes. Refer to the option 3 in the How to Migrate Mailboxes without the ApplicationImpersonation Role? section for details. |
| SharePoint/Office 365 SharePoint Online | Sites.FullControl.All(Have full control of all site collections) | Application | Retrieve settings and permissions of team sites. |
| SharePoint/Office 365 SharePoint Online | TermStore.ReadWrite.All(Read and write managed metadata) | Application | Retrieve and migrate Managed Metadata Service.*Note: The TermStore.ReadWrite.All permission is required to migrate the term set used in the Managed Navigation. If you do not need to migrate the term set used in the Managed Navigation, you can replace the permission with TermStore.Read.All. |
For easy use, you can directly use the following commands to add required API permissions through Manifest.
"requiredResourceAccess": [
{
"resourceAppId": "00000003-0000-0000-c000-000000000000",
"resourceAccess": [
{
"id": "504f21d6-04a7-4fcb-b167-3a299b792828",
"type": "Role"
},
{
"id": "8c07be71-1e68-4c34-9ddc-a9dcdb316eb7",
"type": "Role"
},
{
"id": "25a8297a-fd62-4b6f-a223-3bb94760dab7",
"type": "Role"
},
{
"id": "b8b3793a-307b-47a7-8f35-2168c3bdbce3",
"type": "Role"
},
{
"id": "5b567255-7703-4780-807c-7be8301ae99b",
"type": "Role"
},
{
"id": "62a82d76-70ea-41e2-9197-370581804d09",
"type": "Role"
},
{
"id": "483bed4a-2ad3-4361-a73b-c83ccdbdc53c",
"type": "Role"
},
{
"id": "e6a20c00-0962-428c-b0b8-bf53df771ac7",
"type": "Role"
},
{
"id": "9614ffad-e45d-4be3-8b34-b045d4b913cc",
"type": "Role"
},
{
"id": "51b6b2da-6e13-4281-8a04-23556d7094fe",
"type": "Role"
},
{
"id": "b583af78-bb36-415e-aa81-7311953d3e39",
"type": "Role"
},
{
"id": "beba2506-dc48-4f1e-b8db-bf57502f8a91",
"type": "Role"
},
{
"id": "388e5f2e-1cbd-4b49-8693-b2ea053260de",
"type": "Role"
},
{
"id": "df021288-bdef-4463-88db-98f22de89214",
"type": "Role"
}
]
},
{
"resourceAppId": "00000002-0000-0ff1-ce00-000000000000",
"resourceAccess": [
{
"id": "dc890d15-9560-4a4c-9b7f-a736ec74ec40",
"type": "Role"
},
{
"id": "dc50a0fb-09a3-484d-be87-e023b12c6440",
"type": "Role"
}
]
},
{
"resourceAppId": "00000003-0000-0ff1-ce00-000000000000",
"resourceAccess": [
{
"id": "678536fe-1083-478a-9c59-b99265e6b0d3",
"type": "Role"
},
{
"id": "c8e3537c-ec53-43b9-bed3-b2bd3617ae97",
"type": "Role"
}
]
}
],
Service Account Permissions
If you only use service account authentication for source Teams, the service account must meet the following requirements:
Users with Multi-Factor Authentication (MFA) enabled cannot be used as the service account to perform migrations. You can use a delegated app profile instead.
Additionally, Microsoft has updated API permissions for Microsoft Teams migration. Once the old permissions are deprecated, you can use a delegated app profile to migrate conversations and other Teams data.
What permissions are required if I also use an app profile?
If you use both service account and app profile authentications for source Teams, the service account must meet the following requirements:
Users with Multi-Factor Authentication (MFA) enabled cannot be used as the service account to perform migrations. You can use a delegated app profile instead.
Delegated App Profile Permissions
Fly allows you to use the Fly delegated app profile or custom delegated app profile to connect to your workspace.
The license and permission requirements for the consent user are the same as those for the service account. For details, refer to Service Account Permissions.
If the consent user of the delegated app profile has Multi-Factor Authentication (MFA) enabled, you must authorize or re-authorize the delegated app profile after MFA is enabled. Otherwise, the migration jobs using the delegated app profile will fail.
If you re-authorize the app profile, you need to wait about one hour before using the app profile for your migration to refresh the token when there are permissions updated.
To use the Fly delegated app profile with required permissions, refer to Fly Delegated App Profile Permissions.
To use a custom delegated app profile with required permissions, refer to the following steps:
-
After registering an app in Microsoft Entra ID, add the required permissions to the app. The following sections show the required permissions of different tenants.
-
Click Authentication in the left navigation of the app.
-
Click Add a platform.
-
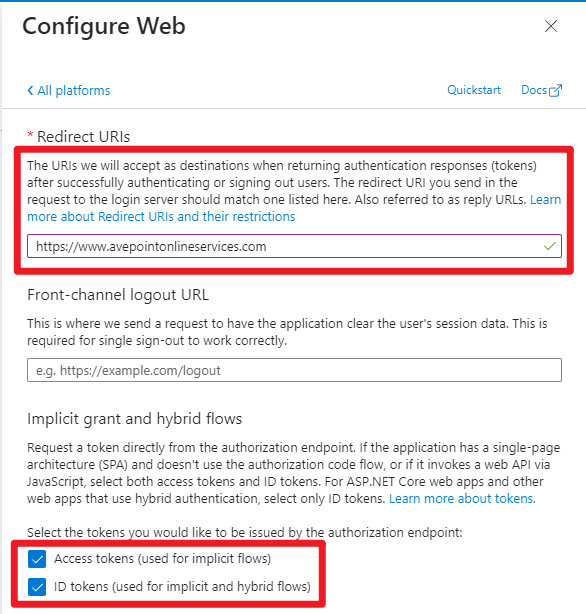
Select Web in the Configure platforms panel.
-
In the Configure Web panel, enter the AvePoint Online Services URL: https://www.avepointonlineservices.com for your commercial environment or https://usgov.avepointonlineservices.com for your U.S. Government environment in the Redirect URIs field.
-
Select the Access tokens and ID tokens checkboxes in the Implicit grant and hybrid flows field.
-
Click Configure.
-
Click Save.
-
Create an app profile for the app using the Custom mode in AvePoint Online Services by referring to .
NOTEWhen consenting to the app, if you have granted the admin consent and allowed public client flows for the permissions, you can choose to use the Global Administrator consent or the User consent method. If not, you can only use the Global Administrator consent method. *Note: When consenting to the app, if you have granted the admin consent and allowed public client flows for the permissions, you can choose to use the Global Administrator consent or the User consent method. If not, you can only use the Global Administrator consent method.
Custom Delegated App Profile (Commercial Tenants)
Make sure the custom delegated app has the following permissions.
| API | Permission | Type | Purpose |
|---|---|---|---|
| Microsoft Information Protection Sync Service | UnifiedPolicy.User.Read(Read all unified policies a user has access to) | Delegated | Only required if you want to manage the sensitivity labels of files/emails/Teams. |
| Azure Rights Management Services | user_impersonation(Create and access protected content for users) | Delegated | Only required if you want to manage the sensitivity labels of files/emails/Teams. |
| SharePoint | AllSites.FullControl(Have full control of all site collections) | Delegated | Retrieve settings and permissions of team sites. |
| SharePoint | TermStore.Read.All(Read managed metadata) | Delegated | Retrieve and migrate Managed Metadata Service. |
| Office 365 Exchange Online | EWS.AccessAsUser.All (Access mailboxes as the signed-in user via Exchange Web Services) | Delegated | Access mailboxes as the signed-in user via Exchange Web Services |
| Office 365 Exchange Online | Exchange.Manage(Manage Exchange configuration) | Delegated | Use Exchange PowerShell to retrieve mailbox permissions. |
| Microsoft Graph | Directory.Read.All(Read directory data) | Delegated | Only required if the source is a multi-geo tenant. |
| Microsoft Graph | Domain.Read.All(Read domains) | Delegated | Retrieve the tenant domain. |
| Microsoft Graph | RoleManagement.Read.Directory(Read directory RBAC settings) | Delegated | Retrieve directory roles. |
| Microsoft Graph | Group.Read.All(Read all groups) | Delegated | Retrieve Microsoft 365 Groups and Group members. |
| Microsoft Graph | Group.ReadWrite.All(Read and write all groups) | Delegated | Required if you only use the delegated app profile and the source consent user is not the Team owner to automatically add the consent user as the Team owner. |
| Microsoft Graph | Sites.Read.All(Read items in all site collections) | Delegated | Retrieve channel folders and files of team sites and private channels’ site collections. |
| Microsoft Graph | User.Read.All(Read all users’ full profiles) | Delegated | Retrieve information of Microsoft 365 user profiles. |
| Microsoft Graph | ChannelMember.Read.All(Read the members of all channels) | Delegated | Retrieve private/shared channel members. |
| Microsoft Graph | ChannelMember.ReadWrite.All(Add and remove members from all channels) | Delegated | Only required the source consent user is not the private/shared channel owner to automatically add the consent user as the channel owner. |
| Microsoft Graph | ChannelMessage.Read.All(Read all channel messages) | Delegated | Retrieve all channel messages. |
| Microsoft Graph | TeamworkTag.Read(Allows the app to read tags in Teams without a signed-in user) | Delegated | Retrieve tags. |
For easy use, you can directly use the following commands to add required API permissions through Manifest.
"requiredResourceAccess": [
{
"resourceAppId": "00000003-0000-0000-c000-000000000000",
"resourceAccess": [
{
"id": "2f9ee017-59c1-4f1d-9472-bd5529a7b311",
"type": "Scope"
},
{
"id": "741c54c3-0c1e-44a1-818b-3f97ab4e8c83",
"type": "Scope"
},
{
"id": "205e70e5-aba6-4c52-a976-6d2d46c48043",
"type": "Scope"
},
{
"id": "a154be20-db9c-4678-8ab7-66f6cc099a59",
"type": "Scope"
},
{
"id": "2eadaff8-0bce-4198-a6b9-2cfc35a30075",
"type": "Scope"
},
{
"id": "0c3e411a-ce45-4cd1-8f30-f99a3efa7b11",
"type": "Scope"
},
{
"id": "767156cb-16ae-4d10-8f8b-41b657c8c8c8",
"type": "Scope"
},
{
"id": "57587d0b-8399-45be-b207-8050cec54575",
"type": "Scope"
},
{
"id": "5f8c59db-677d-491f-a6b8-5f174b11ec1d",
"type": "Scope"
},
{
"id": "4e46008b-f24c-477d-8fff-7bb4ec7aafe0",
"type": "Scope"
},
{
"id": "06da0dbc-49e2-44d2-8312-53f166ab848a",
"type": "Scope"
}
]
},
{
"resourceAppId": "00000012-0000-0000-c000-000000000000",
"resourceAccess": [
{
"id": "c9c9a04d-3b66-4ca8-a00c-fca953e2afd3",
"type": "Scope"
}
]
},
{
"resourceAppId": "870c4f2e-85b6-4d43-bdda-6ed9a579b725",
"resourceAccess": [
{
"id": "34f7024b-1bed-402f-9664-f5316a1e1b4a",
"type": "Scope"
}
]
},
{
"resourceAppId": "00000002-0000-0ff1-ce00-000000000000",
"resourceAccess": [
{
"id": "ab4f2b77-0b06-4fc1-a9de-02113fc2ab7c",
"type": "Scope"
},
{
"id": "3b5f3d61-589b-4a3c-a359-5dd4b5ee5bd5",
"type": "Scope"
}
]
},
{
"resourceAppId": "00000003-0000-0ff1-ce00-000000000000",
"resourceAccess": [
{
"id": "56680e0d-d2a3-4ae1-80d8-3c4f2100e3d0",
"type": "Scope"
},
{
"id": "59a198b5-0420-45a8-ae59-6da1cb640505",
"type": "Scope"
}
]
}
],
Custom Delegated App Profile (GCC High Tenants)
Make sure the custom delegated app profile has the following permissions.
| API | Permission | Type | Purpose |
|---|---|---|---|
| Microsoft Information Protection Sync Service | UnifiedPolicy.User.Read(Read all unified policies a user has access to) | Delegated | Only required if you want to manage the sensitivity labels of files/emails/Teams. |
| Azure Rights Management Services | user_impersonation(Create and access protected content for users) | Delegated | Only required if you want to manage the sensitivity labels of files/emails/Teams. |
| SharePoint | AllSites.FullControl(Have full control of all site collections) | Delegated | Retrieve settings and permissions of team sites. |
| SharePoint | TermStore.Read.All(Read managed metadata) | Delegated | Retrieve and migrate Managed Metadata Service. |
| Office 365 Exchange Online | EWS.AccessAsUser.All (Access mailboxes as the signed-in user via Exchange Web Services) | Delegated | Access mailboxes as the signed-in user via Exchange Web Services |
| Office 365 Exchange Online | Exchange.Manage(Manage Exchange configuration) | Delegated | Use Exchange PowerShell to retrieve mailbox permissions. |
| Microsoft Graph | Domain.Read.All(Read domains) | Delegated | Retrieve the tenant domain. |
| Microsoft Graph | RoleManagement.Read.Directory(Read directory RBAC settings) | Delegated | Retrieve directory roles. |
| Microsoft Graph | Group.Read.All(Read all groups) | Delegated | Retrieve Microsoft 365 Groups and Group members. |
| Microsoft Graph | Group.ReadWrite.All(Read and write all groups) | Delegated | Required if you only use the delegated app profile and the source consent user is not the Team owner to automatically add the consent user as the Team owner. |
| Microsoft Graph | Sites.Read.All(Read items in all site collections) | Delegated | Retrieve channel folders and files of team sites and private channels’ site collections. |
| Microsoft Graph | User.Read.All(Read all users’ full profiles) | Delegated | Retrieve information of Microsoft 365 user profiles. |
| Microsoft Graph | ChannelMember.Read.All(Read the members of all channels) | Delegated | Retrieve private/shared channel members. |
| Microsoft Graph | ChannelMember.ReadWrite.All(Add and remove members from all channels) | Delegated | Only required if the source consent user is not the private/shared channel owner to automatically add the consent user as the channel owner. |
| Microsoft Graph | ChannelMessage.Read.All(Read all channel messages) | Delegated | Retrieve all channel messages. |
| Microsoft Graph | TeamworkTag.Read(Allows the app to read tags in Teams without a signed-in user) | Delegated | Retrieve tags. |
For easy use, you can directly use the following commands to add required API permissions through Manifest.
"requiredResourceAccess": [
{
"resourceAppId": "00000003-0000-0000-c000-000000000000",
"resourceAccess": [
{
"id": "5f8c59db-677d-491f-a6b8-5f174b11ec1d",
"type": "Scope"
},
{
"id": "4e46008b-f24c-477d-8fff-7bb4ec7aafe0",
"type": "Scope"
},
{
"id": "205e70e5-aba6-4c52-a976-6d2d46c48043",
"type": "Scope"
},
{
"id": "a154be20-db9c-4678-8ab7-66f6cc099a59",
"type": "Scope"
},
{
"id": "2eadaff8-0bce-4198-a6b9-2cfc35a30075",
"type": "Scope"
},
{
"id": "0c3e411a-ce45-4cd1-8f30-f99a3efa7b11",
"type": "Scope"
},
{
"id": "767156cb-16ae-4d10-8f8b-41b657c8c8c8",
"type": "Scope"
},
{
"id": "5aefaf00-e921-4a9b-93f2-4a9ff60a2d3a",
"type": "Scope"
},
{
"id": "2f9ee017-59c1-4f1d-9472-bd5529a7b311",
"type": "Scope"
},
{
"id": "741c54c3-0c1e-44a1-818b-3f97ab4e8c83",
"type": "Scope"
}
]
},
{
"resourceAppId": "00000012-0000-0000-c000-000000000000",
"resourceAccess": [
{
"id": "c9c9a04d-3b66-4ca8-a00c-fca953e2afd3",
"type": "Scope"
}
]
},
{
"resourceAppId": "870c4f2e-85b6-4d43-bdda-6ed9a579b725",
"resourceAccess": [
{
"id": "34f7024b-1bed-402f-9664-f5316a1e1b4a",
"type": "Scope"
}
]
},
{
"resourceAppId": "00000002-0000-0ff1-ce00-000000000000",
"resourceAccess": [
{
"id": "ab4f2b77-0b06-4fc1-a9de-02113fc2ab7c",
"type": "Scope"
},
{
"id": "3b5f3d61-589b-4a3c-a359-5dd4b5ee5bd5",
"type": "Scope"
}
]
},
{
"resourceAppId": "00000003-0000-0ff1-ce00-000000000000",
"resourceAccess": [
{
"id": "56680e0d-d2a3-4ae1-80d8-3c4f2100e3d0",
"type": "Scope"
},
{
"id": "59a198b5-0420-45a8-ae59-6da1cb640505",
"type": "Scope"
}
]
}
],
Custom Delegated App Profile (21Vianet Tenants)
Make sure the custom delegated app profile has the following permissions.
| API | Permission | Type | Purpose |
|---|---|---|---|
| Microsoft Information Protection Sync Service | UnifiedPolicy.User.Read(Read all unified policies a user has access to) | Delegated | Only required if you want to manage the sensitivity labels of files/emails/Teams. |
| Microsoft Rights Management Services | user_impersonation(Create and access protected content for users) | Delegated | Only required if you want to manage the sensitivity labels of files/emails/Teams. |
| SharePoint | AllSites.FullControl(Have full control of all site collections) | Delegated | Retrieve settings and permissions of team sites. |
| SharePoint | TermStore.Read.All(Read managed metadata) | Delegated | Retrieve and migrate Managed Metadata Service. |
| Office 365 Exchange Online | EWS.AccessAsUser.All (Access mailboxes as the signed-in user via Exchange Web Services) | Delegated | Access mailboxes as the signed-in user via Exchange Web Services |
| Microsoft Graph | Domain.Read.All(Read domains) | Delegated | Retrieve the tenant domain. |
| Microsoft Graph | RoleManagement.Read.Directory(Read directory RBAC settings) | Delegated | Retrieve directory roles. |
| Microsoft Graph | Group.Read.All(Read all groups) | Delegated | Retrieve Microsoft 365 Groups and Group members. |
| Microsoft Graph | Group.ReadWrite.All(Read and write all groups) | Delegated | Required if you only use the delegated app profile and the source consent user is not the team owner to automatically add the consent user as the team owner. |
| Microsoft Graph | Sites.Read.All(Read items in all site collections) | Delegated | Retrieve channel folders and files of team sites and private channels’ site collections. |
| Microsoft Graph | User.Read.All(Read all users’ full profiles) | Delegated | Retrieve information of Microsoft 365 user profiles. |
| Microsoft Graph | ChannelMember.Read.All(Read the members of all channels) | Delegated | Retrieve private/shared channel members. |
| Microsoft Graph | ChannelMember.ReadWrite.All(Add and remove members from all channels) | Delegated | Only required if the source consent user is not the private/shared channel owner to automatically add the consent user as the channel owner. |
| Microsoft Graph | ChannelMessage.Read.All(Read all channel messages) | Delegated | Retrieve all channel messages. |
| Microsoft Graph | TeamworkTag.Read(Allows the app to read tags in Teams without a signed-in user) | Delegated | Retrieve tags. |
For easy use, you can directly use the following commands to add required API permissions through Manifest.
"requiredResourceAccess": [
{
"resourceAppId": "00000003-0000-0000-c000-000000000000",
"resourceAccess": [
{
"id": "3eef517f-e083-4ef1-92d2-089c3265351d",
"type": "Scope"
},
{
"id": "741c54c3-0c1e-44a1-818b-3f97ab4e8c83",
"type": "Scope"
},
{
"id": "5f8c59db-677d-491f-a6b8-5f174b11ec1d",
"type": "Scope"
},
{
"id": "4e46008b-f24c-477d-8fff-7bb4ec7aafe0",
"type": "Scope"
},
{
"id": "205e70e5-aba6-4c52-a976-6d2d46c48043",
"type": "Scope"
},
{
"id": "a154be20-db9c-4678-8ab7-66f6cc099a59",
"type": "Scope"
},
{
"id": "56c7759e-6add-4129-92a3-d9576dab543c",
"type": "Scope"
},
{
"id": "84160c94-5d27-49e7-a742-2b941e4f2987",
"type": "Scope"
},
{
"id": "c481e8fe-a9d7-435d-8512-63f8e804bd1f",
"type": "Scope"
},
{
"id": "a2d564df-0705-45b6-aa0b-d75d8696bd8f",
"type": "Scope"
}
]
},
{
"resourceAppId": "870c4f2e-85b6-4d43-bdda-6ed9a579b725",
"resourceAccess": [
{
"id": "34f7024b-1bed-402f-9664-f5316a1e1b4a",
"type": "Scope"
}
]
},
{
"resourceAppId": "00000002-0000-0ff1-ce00-000000000000",
"resourceAccess": [
{
"id": "522c3758-e3ef-4482-af45-40e5d9aabd1e",
"type": "Scope"
}
]
},
{
"resourceAppId": "797f4846-ba00-4fd7-ba43-dac1f8f63013",
"resourceAccess": [
{
"id": "41094075-9dad-400e-a0bd-54e686782033",
"type": "Scope"
}
]
},
{
"resourceAppId": "00000003-0000-0ff1-ce00-000000000000",
"resourceAccess": [
{
"id": "56680e0d-d2a3-4ae1-80d8-3c4f2100e3d0",
"type": "Scope"
},
{
"id": "a468ea40-458c-4cc2-80c4-51781af71e41",
"type": "Scope"
}
]
}
],
