Home > Get Started > Enable Replication (Private Preview) > Enable Amazon Web Services (AWS) Replication
Download this articleEnable Amazon Web Services (AWS) Replication
To enable Amazon Web Services replication, complete the following steps:
-
Go to Management > App Management in the AvePoint Online Services interface to create an app profile. For details, refer to Create an App Profile and Grant Consent.
To consent the app, access key of your IAM user is required, for detailed steps on retrieving the access key, refer to Create an Access Key.
-
To protect Elastic Kubernetes Services, if you have limited the public endpoint access, enable the access of reserved IP address of Cloud Backup for IaaS + PaaS. For more details on endpoint access configurations, refer to Modifying cluster endpoint access. For details on downloading the reserved IP address, refer to Download a List of Reserved IP Addresses.
-
After you have completed all the settings above, go to Replication and create replication policies for your AWS services and resources. After defining the protection scope and replication schedule in a policy, you can test or run actual failover jobs when required. Note that you can click the Refresh button in the upper-right corner of the service page to retrieve the latest status for the data to protect.
For details on creating a replication policy and operating failover, refer to Replication (Private Preview).
Create an App Profile and Grant Consent
For the replication of Amazon Web Services, you must create a Cloud Backup for AWS app to connect to your tenant and grant consent for the permissions that this app requests. For details on creating the app, refer to Create an App Profile.
- If your AWS organization contains multiple accounts, make sure to create an IAM user for each account. This ensures proper access to load the VMs associated with each respective account. The connection requires the access key ID and secret access key of an IAM user. The IAM user must have the following permissions:
- kms:\DescribeKey
- kms:ListKeys
- kms:\Decrypt
- kms:Encrypt
- kms:ListAliases
- kms:CreateGrant
- iam:GetPolicyVersion
- iam:ListRoleTags
- iam:RemoveRoleFromInstanceProfile
- iam:CreateRole
- iam:AttachRolePolicy
- iam:\PutRolePolicy
- iam:AddRoleToInstanceProfile
- iam:\DetachRolePolicy
- iam:ListAttachedRolePolicies
- iam:ListRolePolicies
- iam:ListPolicies
- iam:GetRole
- iam:GetPolicy
- iam:ListEntitiesForPolicy
- iam:\DeleteRole
- iam:TagPolicy
- iam:GetRolePolicy
- iam:CreateInstanceProfile
- iam:TagRole
- iam:\DeletePolicy
- iam:ListInstanceProfilesForRole
- iam:\DeleteRolePolicy
- iam:ListPolicyTags
- iam:\DeleteInstanceProfile
- iam:GetInstanceProfile
- iam:ListRoles
- iam:CreatePolicy
- To create an access key for your IAM user for third-party services, refer to Create an Access Key.
- If you want to protect the Amazon EC2 instances with KMS enabled, the IAM user must be added as the key user.
Create an Access Key
To authenticate the requests for backup and restore, you must provide an access key (an access key ID and a secret access key).
Follow the steps below to create an access key for this user:
-
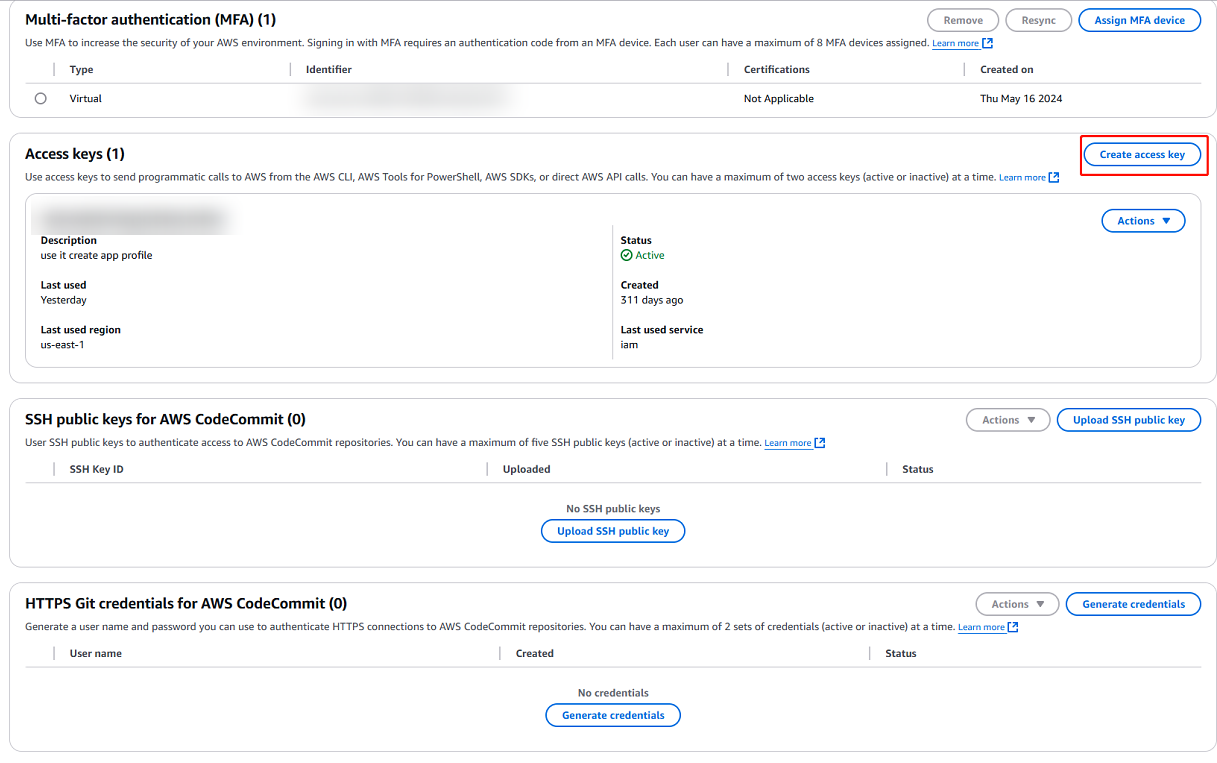
Go to the user details page and expand the Security credentials tab.
-
In the Access keys section, click Create access key.
-
On the Access key best practices & alternatives page, select Third-party service option.
-
In the Retrieve access keys page, copy the access key and the secret access key or choose to download a .csv file to store the information.