Home > Manage App Profiles > Re-authorize an App Profile > Microsoft Tenant > User Consent
Export to PDFUser Consent
The following apps support user consent, and you can re-authorize these apps with a non-Administrator account in your Microsoft tenant.
*Note: When you re-authorize the other apps that are not in the table below, refer to Administrator Consent.
| Service | App type (in AOS) | App name (in Microsoft Entra ID) |
|---|---|---|
| Insights | Insights for Microsoft 365 | AvePoint Insights for Microsoft365 |
| Insights | Insights for Power Platform | AvePoint Insights for Power Platform |
| EnPower | EnPower for Microsoft 365 | AvePoint EnPower for Microsoft365 |
| EnPower | EnPower for Power Platform | AvePoint EnPower PowerPlatform Management |
| EnPower | EnPower for Teams Calling | AvePoint EnPower Teams Calling |
| Fly | Fly for Power Platform | AvePoint Fly for Power Platform |
| Fly | Fly Delegated App | AvePoint Fly Delegated App |
| Cloud Backup for IaaS + PaaS | Cloud Backup for Azure | AvePoint Cloud Backup for Azure |
| Cloud Backup for IaaS + PaaS | Delegated App | AvePoint Online Services – Delegated App |
| Cloud Backup for IaaS + PaaS | Cloud Backup for Azure DevOps | AvePoint Cloud Backup for Azure DevOps |
| Cloud Governance | Cloud Governance for Power Platform | AvePoint Cloud Governance for Power Platform |
| Cloud Governance | Cloud Governance Delegated App | AvePoint Cloud Governance Delegated App |
| MyHub | MyHub | AvePoint MyHub |
| tyGraph | tyGraph Suite | AvePoint tyGraph |
| tyGraph | tyGraph for Viva Engage | AvePoint tyGraph for Viva Engage |
| Cloud Backup for Microsoft 365 | Delegated App | AvePoint Online Services – Delegated App |
| Cloud Backup for Microsoft 365 | Cloud Backup Express | AvePoint Cloud Backup Express |
| Cloud GovernanceCloud Backup for Microsoft 365 | Viva Engage | AvePoint Online Services Administration for Viva Engage |
| Document Management System Online | Document Management System Online (DMS Online) | AvePoint Document Management System Online |
| AvePoint Portal Manager | AvePoint Portal Manager | AvePoint Portal Manager |
| AvePoint Portal Manager | AvePoint Portal Manager for Room - Terminal Interface View | AvePoint Portal Manager for Room - Terminal Interface View |
| EnPowerCloud GovernanceCloud Backup for IaaS + PaaSPolicies for Microsoft 365Insights FlyMyHubtyGraphAvePoint Portal Manager | Custom app with delegated permissions (API Permissions Required by Custom Apps) | [custom app name]You can also get its application ID in the app profile detail page. |
Before you choose the User consent method, complete the following preparations:
-
Ensure that your organization has granted admin consent to the app in Microsoft Entra ID. You can refer to the steps below to grant admin consent to an app:
-
Log in to Microsoft Entra admin center (or Microsoft Azure portal).
-
Follow the instructions below to grant admin consent to an AvePoint app or a custom app:
-
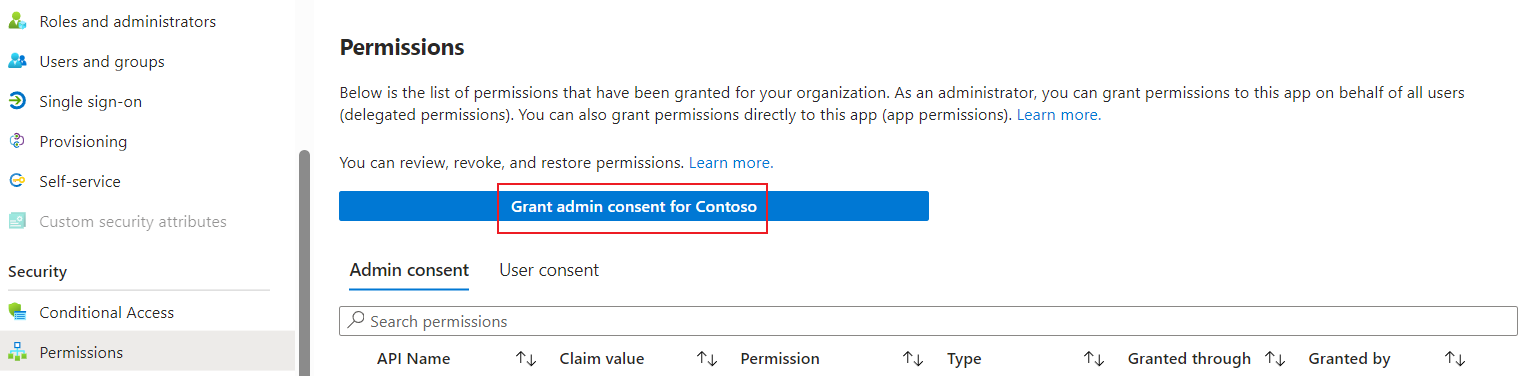
To grant admin consent to an AvePoint app, navigate to Microsoft Entra ID > Enterprise applications, click the app, click Permissions in the Security menu, and then click Grant admin consent for [Tenant name].
-
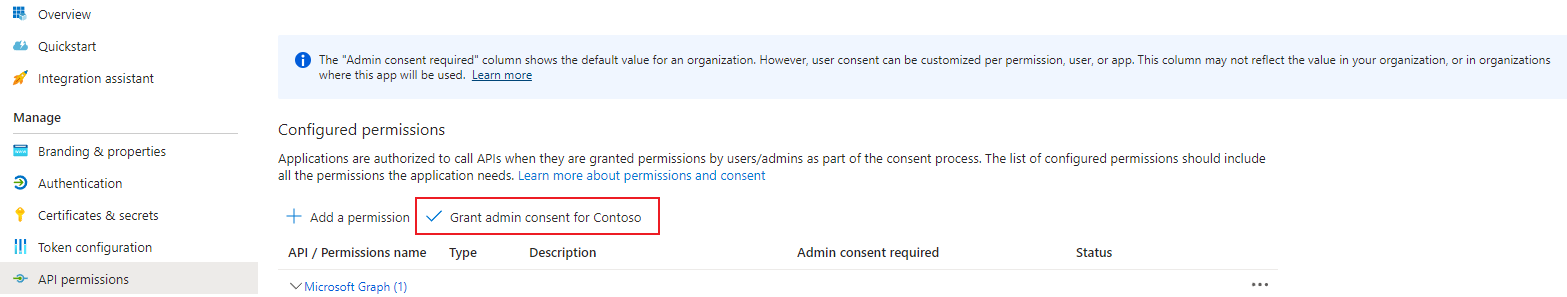
To grant admin consent to a custom app, navigate to Microsoft Entra ID > App registrations, click the app, click API permissions in the Manage menu, and then click Grant admin consent for [Tenant name].
-
-
-
Refer to the following information to prepare required users who consent to the apps:
-
To scan and manage Power Platform objects, the user who provides consent must have the following required license/role:
-
The Power Platform Administrator role must be assigned to the user who provides consent for the app profiles for scanning Environments, Connections, Power Apps, Solutions, Power Automate, or Copilot Studio objects.
-
The Power BI license and Fabric Administrator role must be assigned to the user who provides consent for the app profiles for scanning Power BI objects.
-
-
To re-authorize an AvePoint default service app for Viva Engage, the user who provides consent must have an Engage Administrator (Yammer Administrator in Microsoft Entra ID) role.
-
To re-authorize the Cloud Backup Express app, the user who provides consent to the app must have the Microsoft 365 Backup Administrator role.
-
To re-authorize a custom app for AvePoint Portal Manager, the user who provides consent to the app must have the Teams Service admins role or a higher privileged role.
-
To re-authorize the Cloud Governance delegated app, the user who provides consent to the app must be a group owner.
-
To re-authorize an app profile with the User consent method, refer to the steps below:
-
Select an app profile and click Re-authorize.
-
Note the following when you re-authorize different app profiles:
-
When you re-authorize an app profile for a delegated app used by the Cloud Backup for Microsoft 365 service, you also need to choose the functions which will use this app.
-
When you re-authorize an app profile for a Custom Azure app with delegated permissions app, refer to the following instructions:
-
Application ID – Enter the application ID of the custom app. To keep using the current app, you can get its application ID in the app profile detail page. If you want to change to another app, enter the application ID of the app that your organization has created. For additional details on creating an app, refer to Create a Custom Azure App.
-
Certificate file (.pfx) – Click Browse and select your app’s private certificate (the .pfx file).
*Note: Ensure this .pfx file is paired with the .cer/.crt file which is uploaded for this custom app in Microsoft Entra ID. If your organization does not have any certificates, you can create self-signed certificates by referring to Prepare a Certificate for the Custom Azure App.
-
Certificate password – Enter the password of the certificate.
-
-
-
Select the User consent option.
-
Click Continue to consent.
