Home > Command Centers > AgentPulse > Get Started > Configure AgentPulse Connections
Download this articleConfigure AgentPulse Connections
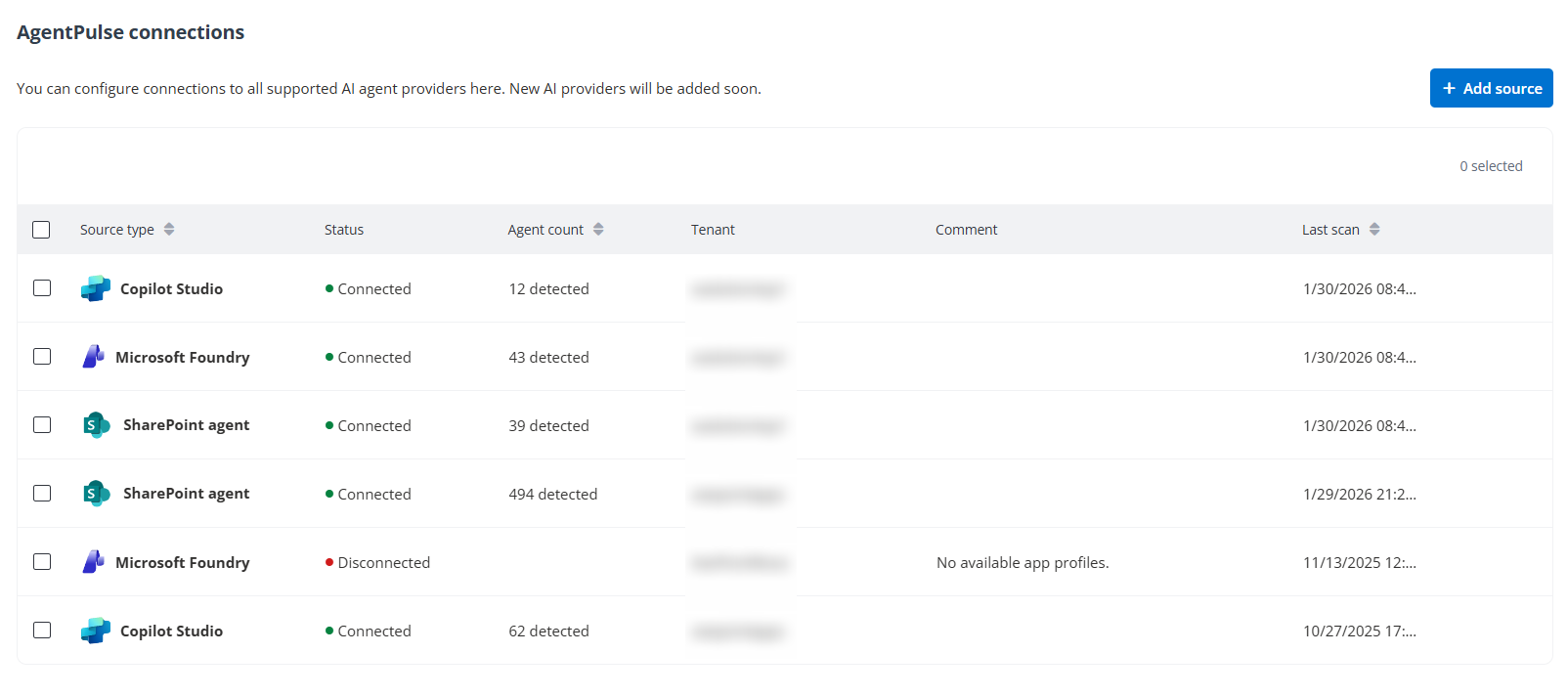
If your organization wants to configure connections to all supported AI agent providers after the onboarding process for AgentPulse completed, service administrators can navigate to Configuration > AgentPulse connections to add sources.
To add a source, refer to the instructions below:
-
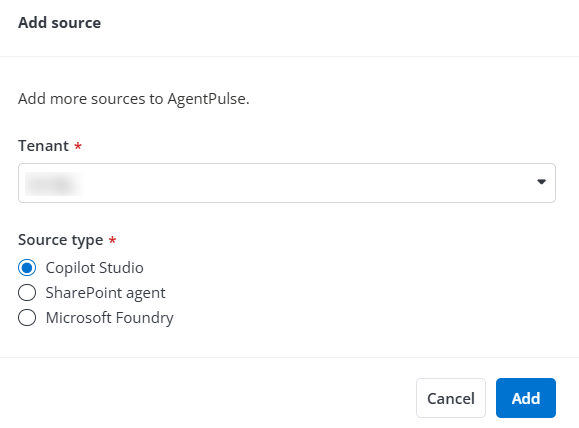
Click Add agent source.
-
Select the platform for which you want to add a source:
-
Microsoft – Select and complete the following configurations to add Microsoft agent sources.
-
Tenant – Select a tenant from the drop-down list.
-
Source type – Select a source type from the drop-down list.
Refer to the table below for the app profiles required by each source type.
Source type Required app profile Copilot Studio AgentPulse SharePoint AgentPulse Microsoft Foundry AgentPulse Microsoft Foundry For the API permissions needed by these app profiles, refer to AgentPulse App Profiles.
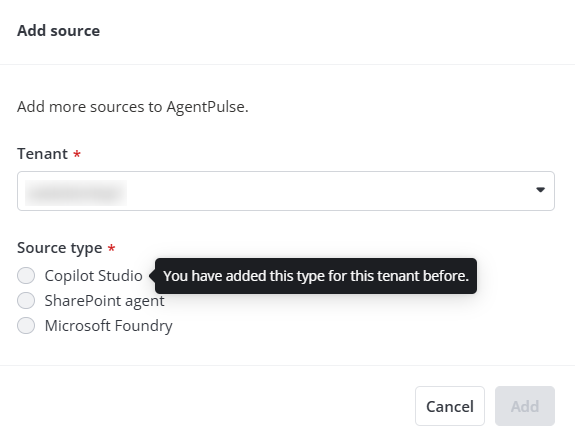
NOTEIf the selected tenant has connected to a source type, the existing source type cannot be selected.
If you need to manually create and configure custom apps with limited permissions, click advanced configuration and complete the following steps to consent to a custom app:
-
If necessary, first Prepare a Certificate for the Custom Azure App.
-
Then, create custom apps by referring to Create a Custom Azure App.
-
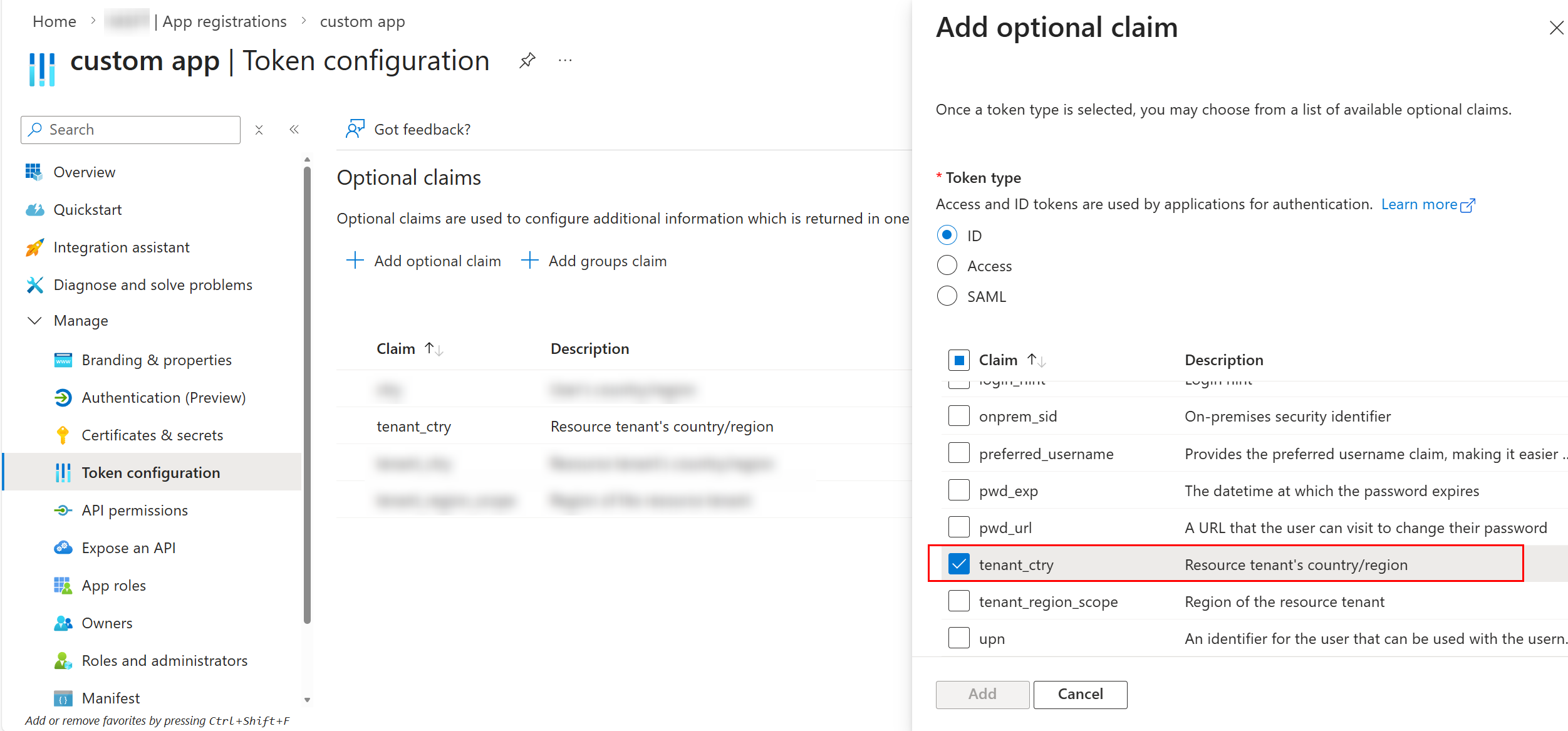
After the custom app is created, navigate to Microsoft Entra admin center > Entra ID > App registrations and complete the following configurations:
-
Select the custom app you created.
-
Under Manage, select Token configuration.
-
Click Add optional claim. In the Add optional claim pane, select Token type as ID.
-
Select tenant_ctry claim, then click Add.
-
-
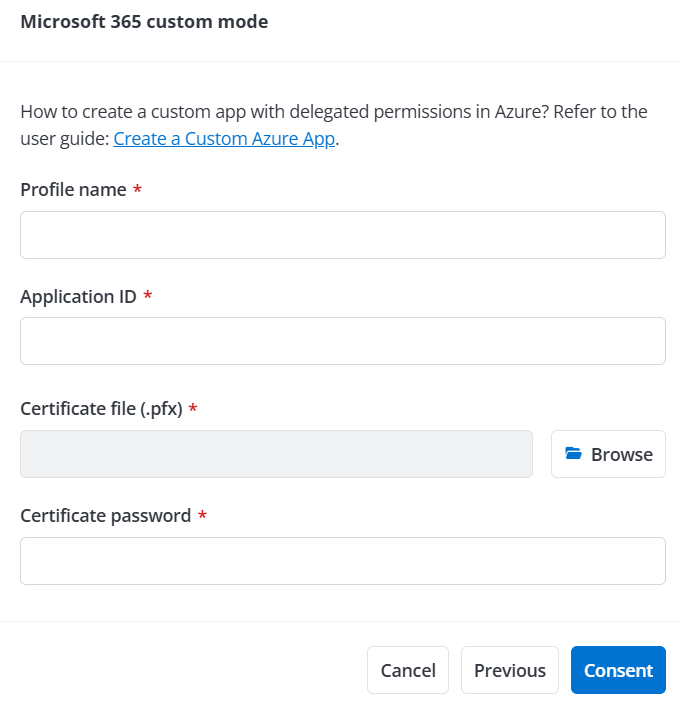
Next, configure app profiles for custom apps in the Microsoft 365 custom mode window by referring to Consent to Custom Azure Apps.
-
Once you’ve completed these steps, click Consent and sign in with a Microsoft 365 Global Administrator account to consent to the app and trigger a scan job for the selected source type.
-
-
Google – Select Google platform and complete the following configurations to add Google agent sources.
NOTEIf the selected tenant has connected to a source type, the existing source type cannot be selected.
-
Select a tenant from the drop-down list.
-
Click Next.
-
Sign in with a Super Admin account that has the following privileges: Users > Read, Groups > Read, and License Management > License Read.
-
In the Register your custom app window, complete the required configurations to consent to a custom app. For detailed instructions on how to create a custom app with delegated permissions in Google, refer to Configure Custom Google App Profiles.
-
Once you’ve completed these steps, click Consent to consent to the app and trigger a scan job for Google agent sources.
-
-
Salesforce – Select and specify a tenant to add Salesforce agent sources. If no tenant is available, refer to Connect Your Salesforce Tenant for detailed instructions on how to connect Salesforce tenants.
NOTE- Salesforce sandbox tenant is not supported.
- You need to set up Salesforce app authentication before connecting your Salesforce tenant. For detailed instructions, refer to Set up Salesforce App Authentication.
-
-
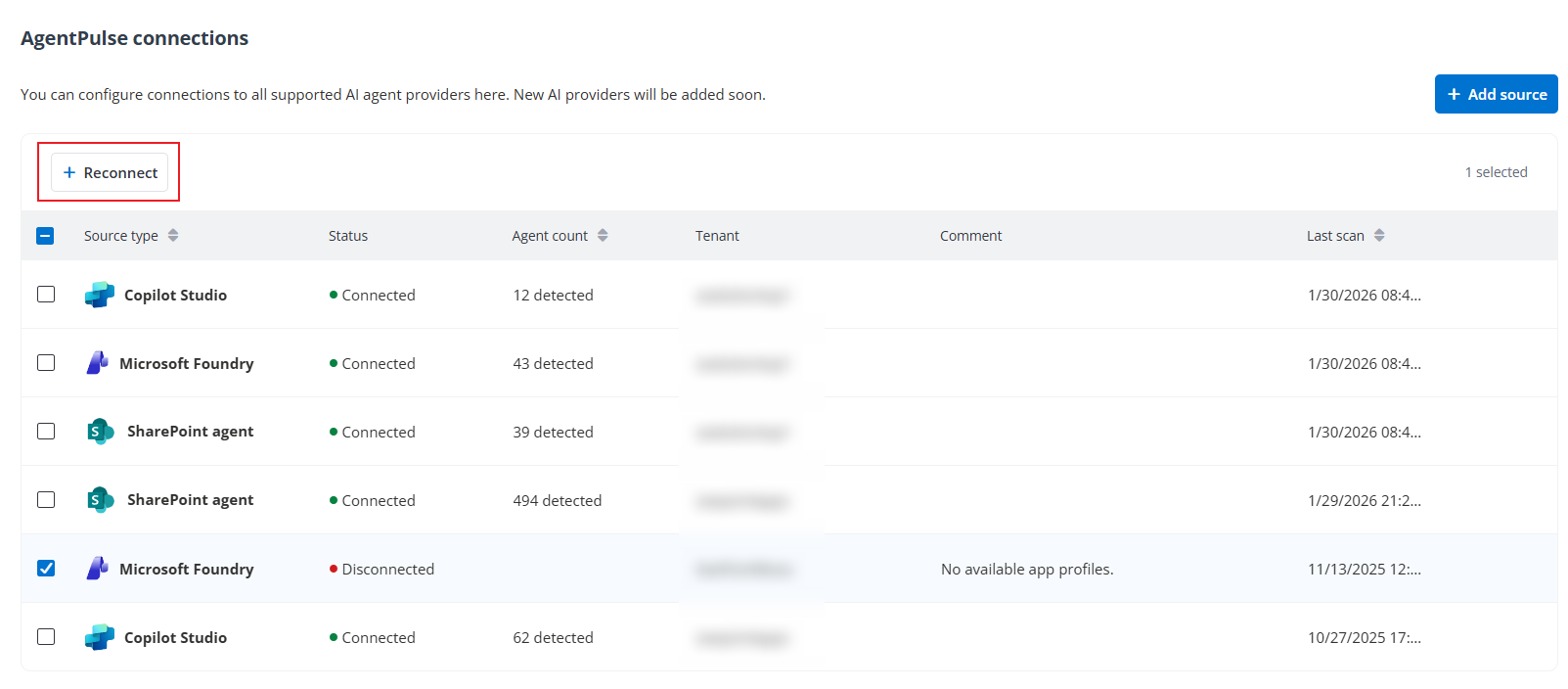
Once you finish the consent, a new connection will be added to the table. Refer to the following information for details of a connection.
-
While a scan job is in progress to scan a source type, the Status column displays Connecting.
-
After a scan job for a source type is completed, the Status column displays Connected, the Agent count column displays the number of objects detected in the job, and the Last scan column displays the time when the scan job is completed.
-
If a scan job is failed, the Status column displays Disconnected, and the Comment column displays the error details. You can select a Disconnected source type and click Reconnect above the table to re-authorize the app profile and run another scan job.
-
Once you finish the consent, you can also view the newly created app profile in Management > App management, and view the newly created scan profile in Auto discovery > Scan profiles.