Home > Required Permissions > App Profile Authentication
Download this articleApp Profile Authentication
If you want to manage Microsoft 365 objects using an app profile, refer to the table below to identify the right app and find its required permissions.
To use rules related to Exchange mailbox and Security and distribution group object types, you must assign the Exchange Administrator role to the app in the Microsoft Entra admin center. To find rules where the Exchange Administrator role is required, refer to Supported Rules for Service Level Policies and Supported Rules for Tenant Level Policies. For the detailed instructions on how to assign the Exchange Administrator role to the app, refer to Assign Exchange Administrator Role to Azure App.
To use the Teams Tagging Settings rule, you must assign the Teams Administrator role to the app in the Microsoft Entra admin center. For the detailed instructions on how to assign the Teams Administrator role to the app, refer to Assign Teams Administrator Role to Azure App.
Make sure the account used to consent to or re-authorize the app profile has the Microsoft 365 Global Administrator or Privileged Role Administrator role.
Setup Methods and App Types
The table below lists the supported setup methods and app types. For details on creating app profiles in AvePoint Online Services, refer to App Management.
| Setup Method | App Type | Note |
|---|---|---|
| Modern Mode (Recommended) | Policies for Microsoft 365 | Once you create this app profile, the AvePoint Policies for Microsoft365 app will be automatically created in your Microsoft Entra ID. To see the API permissions you need to accept when you authorize the app, refer to Policies for Microsoft 365. |
| Modern Mode (Recommended) | Reporting for Microsoft 365 | Once you create this app profile, the AvePoint Reporting for Microsoft365 app will be automatically created in your Microsoft Entra ID. To see the API permissions you need to accept when you authorize the app, refer to Reporting for Microsoft 365. |
| Classic Mode | Microsoft 365 (All permissions) | Once you create this app profile, the AvePoint Online Services Administration for Microsoft365 app will be automatically created in your Microsoft Entra ID. To see the API permissions you need to accept when you authorize the app, refer to Microsoft 365 (All Permissions). |
| Classic Mode | Microsoft Entra ID | Once you create this app profile, the AvePoint Online Services Administration for Microsoft Entra ID app will be automatically created in your Microsoft Entra ID. To see the API permissions you need to accept when you authorize the app, refer to Microsoft Entra ID. |
| Custom Mode | Custom Azure App | You need to create an app in your Microsoft Entra ID and create an app profile for the app in AvePoint Online Services. To see the API permissions required by Policies for Microsoft 365, refer to Permissions for Custom Azure App. |
Permissions for Custom Azure App
If you want to create a custom Azure app to connect AvePoint Online Services to your Microsoft 365 tenant and Microsoft Entra ID, refer to the API permissions listed in the following table to add the API permissions required by Policies for Microsoft 365 to your custom Azure app.
| API | Type | Permission | Purpose | Which Rules Need This |
|---|---|---|---|---|
| SharePoint | Application | Sites.FullControl.All (Have full control of all site collections) | Retrieve and update the information on site collections and groups/teams’ sites. | Rule Table 1 |
| SharePoint | Application | User.Read.All (Read user profiles) | Retrieve user profiles for OneDrive that are scanned by AvePoint Online Services. | This permission is not required by rules in Policies for Microsoft 365. It is required for auto discovery scan profiles in AvePoint Online Services. |
| Microsoft Graph | Application | AuditLog.Read.All (Read all audit log data) | Read all audit logs | Rule Table 2 |
| Microsoft Graph | Application | ChannelMember.ReadWrite.All (Add and remove members from all channels) | Add and remove members from all channels | Rule Table 3 |
| Microsoft Graph | Application | User.Read.All (Read all users' full profiles) | Read all users’ settings used by rules; Retrieve user information for people pickers, Defined Groups, and filters. | Rule Table 4 |
| Microsoft Graph | Application | User.ReadWrite.All (Read and write all users’ full profiles) | Read and write users’ settings | Rule Table 5 |
| Microsoft Graph | Application | Group.Read.All (Read all groups) | Read groups’ members and settings used by rules; Retrieve group information for people pickers, Defined Groups, and filters. | Rule Table 6 |
| Microsoft Graph | Application | Group.ReadWrite.All (Read and write all groups) | Update groups’ members and settings | Rule Table 7 |
| Microsoft Graph | Application | Channel.ReadBasic.All (Read the names and descriptions of all channels) | Retrieve the number of private channel owners. | Rule Table 8 |
| Microsoft Graph | Application | Directory.ReadWrite.All (Read and write data in organization’s directory) | Read and write users and groups data in the organization’s directory. | Rule Table 9 |
| Microsoft Graph | Application | TeamSettings.ReadWrite.All (Read and change all teams' settings) | Update Teams' settings. | Rule Table 10 |
| Microsoft Graph | Application | Channel.Delete.All (Delete channels) | Delete channels. | Rule Table 11 |
| Microsoft Graph | Application | Files.Read.All (Read files in all site collection) | Read files in site collections. | Rule Table 12 |
| Microsoft Graph | Application | TeamMember.ReadWrite.All (Add and remove members from all teams) | Add and remove teams' members. | Rule Table 13 |
| Microsoft Information Protection Sync Service | Application | UnifiedPolicy.Tenant.Read (Read all unified policies of the tenant) | Retrieve information of published sensitivity labels from Microsoft 365. | Rule Table 14 |
| Office 365 Exchange Online | Application | Exchange.ManageAsApp (Manage Exchange As Application) | Retrieve and manage Exchange Online mailboxes. | Rule Table 15 |
| Azure Rights Management Services Make sure your organization has a subscription (or service principal) for the Azure Rights Management Services API. For 21Vianet tenants, the API name is Microsoft Rights Management Services. | Application | Content.SuperUser (Read all protected content for this tenant) | Retrieve sensitivity labels in your organization and apply sensitivity labels to files. | Rule Table 16 |
| Azure Rights Management Services Make sure your organization has a subscription (or service principal) for the Azure Rights Management Services API. For 21Vianet tenants, the API name is Microsoft Rights Management Services. | Application | Content.Writer (Create protected content) | Retrieve sensitivity labels in your organization and apply sensitivity labels to files. | Rule Table 17 |
Permissions Overview by Rules
The following tables list the rules that need the required permissions.
Rule Table 1
| Rule Name | Rule Description |
|---|---|
| Access Requests Settings | Control access requests settings, including options to allow members to share content and to allow access requests. |
| Content Creation and Upload Restriction | Control content creation and upload including items, attachments, and documents based on user, size, file extension, content type, and sensitivity label. |
| Classification Enforcement | Enforce that all Groups or Teams have a classification assigned to them and assign a default classification if there is none. |
| Control Access from Unmanaged Devices | Block or limit access to SharePoint and OneDrive content from unmanaged devices. |
| Content Sensitivity Label Enforcement | Enforce sensitivity labels for documents based on their risk level, sensitivity level, and exposure level. |
| Deletion Restriction | Control users who have the ability to delete objects in sites. |
| Guest User Access Enforcement | Control users who have the ability to add guest users to Groups or Teams. |
| Guest User Full Control Permission Restriction | Report guest users who have the site-level Full Control permission and remove this permission from them. |
| Ghost Guest User Detection | Detect guest users who do not have permissions to any SharePoint site and are not members of any Microsoft 365 Group, Team, security group, or distribution list. |
| Library Default Sensitivity Label Enforcement | Enforce a default sensitivity label for document libraries so that the sensitivity label will be applied to all newly created or edited Office files. |
| Library Versioning Settings Enforcement | Enforce the versioning settings for all libraries in sites. |
| List/Library Creation Restriction | Control users who have the ability to create lists and libraries. |
| List/Library Object Number Restriction | Control the number of items, documents, and folders in a list/library. |
| Permission Inheritance Protection | Protect permission inheritance from being broken at specific object levels. |
| Permission Level Enforcement for Built-in SharePoint Groups | Enforce permission levels for built-in SharePoint groups, including site owners, site members, and site visitors. |
| Pre-defined Group Members (Cloud Governance) | Ensure users you have defined via site collection properties (example: Cloud Governance site contacts) belong to the designated SharePoint groups. |
| Remove Shadow Users | Remove users who have access to the SharePoint site but are not part of the Group/Team membership. |
| Restrict Sharing Links | Restrict sharing links that are created by or shared with specific users and groups. |
| Restrict Sharing Links with Edit Permission | Restrict sharing links with Edit permission that are created by or shared with specific users and groups. |
| Scan External Users | Scan external users in sites where external sharing is disabled. |
| Scan Orphaned Users | Scan users or groups that have been deleted or blocked in your Microsoft Entra ID. |
| Search and Offline Availability Enforcement | Control whether site content can be searched or downloaded to offline clients |
| Shared Channel Creation Restriction | Control users who have the ability to create shared channels inside Teams. |
| SharePoint Group Membership Enforcement | Enforce specific users to be in the owners, members, or visitors group of a site. |
| Sharing Link Expiration Enforcement | Enforce the duration of how long sharing links remain active after being created in sites. |
| SharePoint Permission Enforcement | Control permission levels for the specified users and groups on SharePoint sites. |
| Site Collection Administrator Enforcement | Enforce specific users and groups to be in the Site Collection Administrators group of a site. |
| Site Collection Administrator Number Restriction | Control the number of site collection administrators in a site. |
| Site Owner Number Restriction | Control the number of site owners in a site. |
| Site Owner Restriction | Control users who can be added to the owner group of a site. |
| Site Sensitivity Label Enforcement | Enforce a defined sensitivity label on sites and remove any existing ones. |
| Site Storage Enforcement | Enforce storage limit for sites. |
| Teams Settings Enforcement | Enforce certain Teams settings. |
| User/Group Restriction | Control users and groups that can be added to sites. |
| User Permission Replacement | Report or remove permissions from a specific user and assign the permissions to other designated users. |
Rule Table 2
| Rule Name | Rule Description |
|---|---|
| Inactive Guest User Detection | Detect guest users who do not have any activities in SharePoint sites, Groups, and Teams for a defined period of time. |
Rule Table 3
| Rule Name | Rule Description |
|---|---|
| Private Channel Owner Number Restriction | Control the number of owners in Teams private channels. |
| Private Channel Ownership Enforcement | Enforce specific users to be owners of Teams private channels. |
| Shared Channel Ownership Enforcement | Enforce specific users to be owners of Teams shared channels. |
Rule Table 4
| Rule Name | Rule Description |
|---|---|
| Classification Enforcement | Enforce that all Groups or Teams have a classification assigned to them and assign a default classification if there is none. |
| Groups/Teams Creation Restriction | Control users who have the ability to create Groups or Teams. |
| Groups/Teams Deletion Restriction | Control users who have the ability to delete Groups or Teams. |
| Guest User Access Enforcement | Control users who have the ability to add guest users to Groups or Teams. |
| Membership Restriction | Control users who can be added to Microsoft 365 Groups, Teams, security groups, or distribution lists as members. |
| Member Number Restriction | Control the number of members in Microsoft 365 Groups, Teams, security groups, or distribution lists. |
| Ownership Enforcement | Enforce specific users to be in the owner group of a site. |
| Ownership Restriction | Control users who can be added to Groups or Teams as owners. |
| Scan External Users | Scan external users in sites where external sharing is disabled. |
| Teams Settings Enforcement | Enforce certain Teams settings. |
This permission is also required by common features, including people pickers, Defined Groups, and filters.
Rule Table 5
| Rule Name | Rule Description |
|---|---|
| Ghost Guest User Detection | Detect guest users who do not have permissions to any SharePoint site and are not members of any Microsoft 365 Group, Team, security group, or distribution list. |
| Inactive Guest User Detection | Detect guest users who do not have any activities in SharePoint sites, Groups, and Teams for a defined period of time. |
| Remove Licenses from Inactive Users | Remove licenses from users who do not have activities in Microsoft 365 services for a certain period. |
| Remove Licenses from Blocked Users | Remove licenses from users who have been blocked from signing in. |
This permission will be required if you want to use the auto-fix violations feature in rules to automatically fix out-of-policy settings when violations are identified. Without granting this permission to make the auto-fix violations feature available, you can manually fix the out-of-policy settings.
Rule 6
| Rule Name | Rule Description |
|---|---|
| Owner Number Restriction | Control the number of owners in Microsoft 365 Groups, Teams, security groups, and distribution lists. |
| Ghost Guest User Detection | Detect guest users who do not have permissions to any SharePoint site and are not members of any Microsoft 365 Group, Team, security group, or distribution list. |
This permission is also required by common features, including people pickers, Defined Groups, and filters.
Rule Table 7
| Rule Name | Rule Description |
|---|---|
| Classification Change Restriction | Prevent changes to the classification of Groups or Teams. |
| Classification Enforcement | Enforce that all Groups or Teams have a classification assigned to them and assign a default classification if there is none. |
| Control Group Visibility in Global Address List | Control the visibility of mail-enabled security groups and distribution lists in the global address list. |
| Groups/Teams Creation Restriction | Control users who have the ability to create Groups or Teams. |
| Groups/Teams Deletion Restriction | Control users who have the ability to delete Groups or Teams. |
| Groups/Teams Name Enforcement | Prevent owners of Groups or Teams from changing their Group or Team name. |
| Guest User Access Enforcement | Control users who have the ability to add guest users to Groups or Teams. |
| Membership Restriction | Control users who can be added to Microsoft 365 Groups, Teams, security groups, or distribution lists as members. |
| Member Number Restriction | Control the number of members in Microsoft 365 Groups, Teams, security groups, or distribution lists. |
| Microsoft 365 Group Visibility in Outlook Client | Control if a Microsoft 365 Group is visible in the Outlook client. |
| Ownership Restriction | Control users who can be added to Groups or Teams as owners. |
| Privacy Restriction | Control the privacy settings of Groups or Teams. |
| Restrict Member Invitations | Control users who have the ability to add users to Groups or Teams. |
| Restrict Member Removal | Control users who have the ability to remove members from Microsoft 365 Groups or Teams. |
| Teams Settings Enforcement | Enforce certain Teams settings. |
| User Restriction | Enforce that specific users can only be assigned membership of the specified Groups/Teams. |
Besides, this permission will be required if you want to use the auto-fix violations feature in rules to automatically fix out-of-policy settings when violations are identified. Without granting this permission to make the auto-fix violations feature available, you can manually fix the out-of-policy settings.
Rule Table 8
| Rule Name | Rule Description |
|---|---|
| Private Channel Ownership Enforcement | Enforce specific users to be owners of Teams private channels. |
| Private Channel Owner Number Restriction | Control the number of owners in Teams private channels. |
| Shared Channel Creation Restriction | Control users who have the ability to create shared channels inside Teams. |
| Shared Channel Ownership Enforcement | Enforce specific users to be owners of Teams shared channels. |
Rule Table 9
| Rule Name | Rule Description |
|---|---|
| Groups Guest Access Restriction | Control whether people outside your organization can be invited as guests and access group content. |
| Teams Tagging Settings | Control how tags are used across your organization. |
Rule Table 10
| Rule Name | Rule Description |
|---|---|
| Shared Channel Creation Restriction | Control users who have the ability to create shared channels inside Teams. |
| Teams Settings Enforcement | Enforce certain Teams settings. |
Rule Table 11
| Rule Name | Rule Description |
|---|---|
| Shared Channel Creation Restriction | Control users who have the ability to create shared channels inside Teams. |
Rule Table 12
| Rule Name | Rule Description |
|---|---|
| Shared Channel Creation Restriction | Control users who have the ability to create shared channels inside Teams. |
Rule Table 13
| Rule Name | Rule Description |
|---|---|
| Private Channel Ownership Enforcement | Enforce specific users to be owners of Teams private channels. |
Rule Table 14
| Rule Name | Rule Description |
|---|---|
| Content Creation and Upload Restriction | Control content creation and upload including items, attachments, and documents based on user, size, file extension, content type, and sensitivity label. |
| Content Sensitivity Label Enforcement | Enforce sensitivity labels for documents based on their risk level, sensitivity level, and exposure level. |
| Library Default Sensitivity Label Enforcement | Enforce a default sensitivity label for document libraries so that the sensitivity label will be applied to all newly created or edited Office files. |
| Site Sensitivity Label Enforcement | Enforce a defined sensitivity label on sites and remove any existing ones. |
Rule Table 15
| Rule Name | Rule Description |
|---|---|
| Automatic Forwarding Restriction | Restrict users from auto-forwarding emails. |
| Bypass Spam Filtering Rule Restriction | Restrict users from creating the mail flow rule to skip spam filtering when receiving emails from specific domains. |
| Control Anonymous Calendar Sharing | Control whether users are allowed to share their calendars with anonymous users outside the organization. |
| Control Exchange Online PowerShell Access for Non-administrators | Control Exchange Online PowerShell access for non-administrators. |
| Control Focused Inbox | Control whether to enable the focused inbox view for users. |
| Control Group Visibility in Global Address List | Control the visibility of mail-enabled security groups and distribution lists in the global address list. |
| Control Mailbox Auditing for All Users | Control whether to enable mailbox auditing for all users. |
| Control Plus Addressing | Control whether users can use plus addressing to quickly create custom email addresses based on their standard email addresses. |
| Control Sending Emails from Aliases | Control whether users are allowed to send emails from aliases. |
| Deleted Item Retention Period Enforcement | Set the retention period that permanently deleted mailbox items are kept in the Recoverable Items folder. |
| DKIM Signature Enforcement | Sign emails with DKIM (Domain Keys Identified Mail) signatures for your domains to help recipients ensure the identities of senders. |
| International Spam Prevention | Prevent email messages that are written in specific languages or sent from specific countries or regions. |
| Legacy Email Protocols Restriction | Restrict the use of legacy email protocols, including POP, SMTP, and IMAP protocols, to prevent password spray attacks that may breach mailboxes in your tenants. |
| Malware Prevention | Protect your organization from malware by quarantining email messages where malware is detected. |
| Message Size Restriction | Restrict the maximum size for messages sent and received by mailboxes. |
| Outlook External Email Tag Enforcement | Choose whether to add tags to external emails in Outlook to help users identify emails from external senders. |
| Owner Number Restriction | Control the number of owners in Microsoft 365 Groups, Teams, security groups, and distribution lists. |
| Outbound Spam Prevention | Protect your organization from outbound spam. |
| Rich-Text Format Restriction | Restrict the rich-text format in emails to prevent malformed emails sending to other users. |
| Shared Mailbox Sign-In Restriction | Control whether to allow users to sign in to the shared mailboxes by their associated user accounts. |
Rule Table 16
| Rule Name | Rule Description |
|---|---|
| Content Sensitivity Label Enforcement | Enforce sensitivity labels for documents based on their risk level, sensitivity level, and exposure level. |
Rule Table 17
| Rule Name | Rule Description |
|---|---|
| Content Sensitivity Label Enforcement | Enforce sensitivity labels for documents based on their risk level, sensitivity level, and exposure level. |
Specific Operations for Microsoft 365 U.S. Government
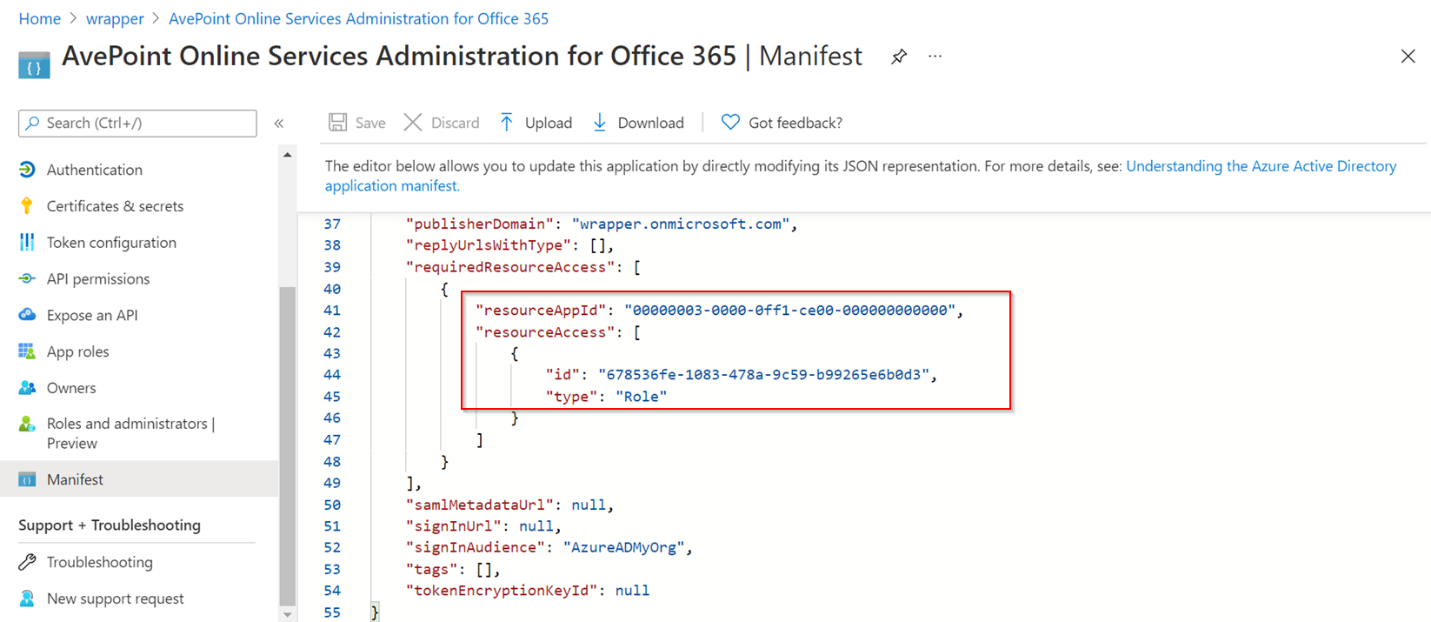
If you are using a Microsoft 365 U.S. Government environment and you want to use a custom Azure app for Microsoft 365 management, you must add SharePoint API permissions to the custom app through Manifest. Microsoft Azure Government does not allow you to select SharePoint API permissions on the Azure Governance Portal interface.
| API | Permission | resourceAppId | id | type |
|---|---|---|---|---|
| SharePoint | Sites.FullControl.All (Have full control of all site collections) | 00000003-0000-0ff1-ce00-000000000000 | 678536fe-1083-478a-9c59-b99265e6b0d3 | Role |
Microsoft Graph API Beta Version in Use
Policies for Microsoft 365 leverages Microsoft Graph beta APIs (the APIs in preview) for some operations that are currently unsupported by version v1.0. The features using the following beta APIs may be affected if Microsoft introduces changes to their beta APIs.
Refer to the table below for the beta version API methods that Policies for Microsoft 365 uses.
| API | Type | API URL | Permission | Purpose |
|---|---|---|---|---|
| Microsoft Graph | Application | https://graph.microsoft.com/beta/users | User.Read.All (Read all users' full profiles) | Comment 1 |
| Microsoft Graph | Application | https://graph.microsoft.com/beta/security/informationProtection/sensitivityLabels | InformationProtectionPolicy.Read.All (Read all published labels and label policies for an organization) | Comment 2 |
Comment 1:
- Defined Group: Custom property
Comment 2:
-
Filter: Sensitivity label
-
Rule: Content Creation and Upload Restriction
-
Rule: Content Sensitivity Label Enforcement
-
Rule: Library Default Sensitivity Label Enforcement
-
Rule: Site Sensitivity Label Enforcement